What is Smishing and how to protect yourself from it?

Bisma Farrukh

In today’s digital age, you’re likely familiar with various cybersecurity threats. However, one increasingly prevalent danger may have escaped your notice: smishing. This malicious tactic combines “SMS” and “phishing“.
Smartphones have made banking, shopping, and two-factor codes as easy as glancing at a text and exactly why cyber-crooks love smishing. In 2025, SMS-based phishing accounts for nearly 4 in 10 mobile threats and has jumped more than 300 percent since last year. Unlike email scams that often get trapped by filters, smishing lands right in your pocket sounding urgent, personal, and trustworthy.
Understanding smishing and how to protect yourself is crucial in safeguarding your data and financial well-being. In this article, you’ll learn about the nature of smishing attacks, common techniques employed by scammers, and essential steps to fortify your defenses against this growing threat.
Table of Contents
What is Smishing in cybersecurity?
Smishing is a phishing attack that uses SMS (Short Message Service), text messages, or messaging apps to deceive individuals into revealing personal or financial information, downloading malicious apps, or clicking on harmful links. The term “smishing” combines SMS and phishing, highlighting its method of delivery and underlying intent: social engineering through deceptive communication.
Unlike traditional phishing, which primarily occurs over email, smishing targets your mobile device, making it more immediate, personal, and often harder to detect. With the widespread use of smartphones and people’s tendency to trust text messages more than emails, cybercriminals have turned smishing into a highly effective attack vector.
According to TheSun: The FBI warns over 150 million U.S. iPhone and Android users to delete suspicious texts, after an 800% spike in malicious DMV-related smishing messages reported in June 2025
How does Smishing Work?
Smishing is defined as operating by exploiting your trust in text messages. Cybercriminals send deceptive SMS messages that appear to be from legitimate sources, such as banks or government agencies. These texts often contain urgent requests or enticing offers, prompting you to click on malicious links or provide sensitive information.
By trusting: Once you interact, attackers can steal your data, install malware on your device, or gain unauthorized access to your accounts. Smishing’s effectiveness lies in its ability to bypass traditional email security measures and capitalize on the immediate nature of text messaging.
By context: Attackers typically want the recipient to open a URL link within a text message. The link leads to a phishing tool that prompts recipients to disclose private information. This phishing tool often takes the form of a website or app that poses as a false identity.
By providing info: Targets are selected in various ways, often based on their affiliation with an organization or regional location. This includes employees or customers of a specific institution, mobile network subscribers, university students, and residents of a particular area.
Types of Smishing Attacks
Smishing attacks come in various forms, each designed to exploit different vulnerabilities. Understanding these types can help you better protect yourself against potential threats.
1. Phishing Links to Fraudulent Websites
This is the most prevalent form of smishing, where attackers send text messages containing links that lead to spoofed websites designed to mimic legitimate services. These sites often replicate banking portals, email logins, or subscription services, tricking users into entering their credentials or financial details.
Here’s an example:
“Your PayPal account has been restricted. Verify your information to restore access: [malicious link]”
2. Fake Delivery Notifications
With the rise of online shopping, fake shipping alerts have become a go-to tactic for attackers. These messages impersonate well-known delivery services, such as DHL, FedEx, or UPS, and claim there’s an issue with a package delivery. Victims are prompted to click a link or provide additional information, often leading to phishing sites or malware downloads.
3. Banking and Financial Alerts
In this variant, attackers impersonate banks or financial institutions, warning recipients about suspicious activity or urging them to confirm a transaction. These messages are designed to provoke anxiety, prompting users to act without questioning the message’s authenticity.
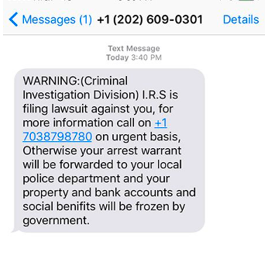
4. Government and Tax-Related Scams
Cybercriminals often exploit authority by impersonating government agencies, especially during tax season or major regulatory changes. These messages may reference tax refunds, penalties, or benefits, coaxing individuals into clicking malicious links or sharing sensitive information.
5. Tech Support and Subscription Scams
Attackers may send messages falsely claiming that a user’s subscription to a software or service, such as antivirus software or a VPN, has been renewed or is about to expire. Victims are instructed to call a support number or click a link to cancel, often leading to fake representatives who request remote access or personal details.
6. Urgent Personal or Workplace Requests
This type of smishing leverages social engineering by pretending to be a trusted contact—such as a friend, family member, or company executive, asking for immediate help. Messages may request money transfers, gift cards, or sensitive internal data.
7. Promotional Scams and Fake Prize Offers
These smishing attempts entice users with offers of prizes, discounts, or exclusive deals—only to redirect them to phishing sites or malicious downloads. Often, they ask for a small “processing fee” or personal details under the guise of claiming the reward.
Example of how a promotional scam looks:
“You’ve won a $500 Amazon gift card! Claim your reward now before it expires: [phishing link]”
Smishing Examples
Here are some more examples of smishing text messages you should be wary of:
COVID-19 Vaccine Scam
Many have instantly spotted this scam since there is no online test for COVID-19. However, the premise of these smishing attacks may easily evolve as preying on pandemic fears is an effective method of victimizing the public.
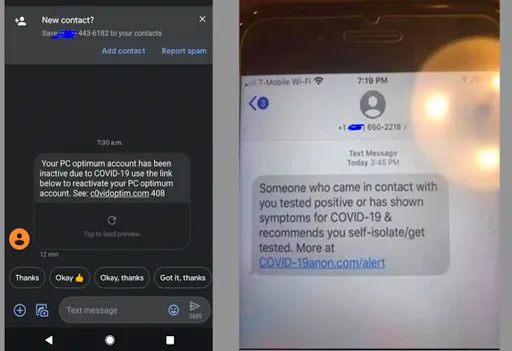
Fake IRS tax refund Scam messages
In this scheme, scammers send text messages claiming to be from the IRS, informing recipients of an unexpected tax refund. The message typically includes a link or a phone number to claim the refund. Once the victim clicks the link or contacts the provided number, they may be asked to provide personal information such as Social Security numbers, bank account details, or other sensitive data. This can lead to identity theft, financial fraud, or unauthorized access to personal accounts.
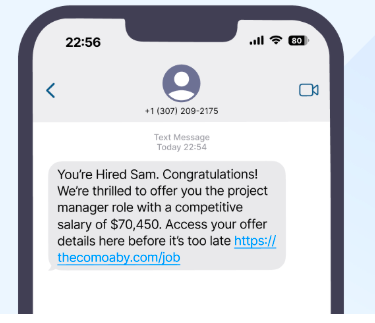
Fake Job offers
Another prevalent smishing tactic involves sending unsolicited text messages offering lucrative job opportunities with attractive benefits. These messages may promise high pay, flexible hours, or work-from-home options to entice recipients. To proceed with the supposed job application or interview process, victims may be prompted to provide personal information, such as their full name, address, Social Security number, or even payment for training materials or background checks.
Some other Examples of Smishing
“There is an issue with your bank account. Please click here to verify your login details.”
This is a common scam that aims to steal your banking login information. Do not click any links in suspicious texts.
“Your recent order has been delayed. Confirm your details using this link to track your package.”
Smishing scams often pretend to be from delivery companies to trick you into sharing personal information. Ignore these texts, and do not click the link.
“A payment you made failed. Please update your billing info immediately.”
Smishing scams often claim an issue with a recent payment to get you to provide sensitive data. Ignore these texts and do not provide any account details.
“Your password needs to be updated for security reasons. Update now at this link.”
No legitimate company will ask you to update your password through a text message link. This is a phishing attempt. Do not click the link or provide any login information.
“Your account will be suspended within 24 hours if you do not confirm your details.”
This is a scare tactic used in smishing scams. Do not respond or click any links, and ignore the text message.
Business Impact of Smishing
Smishing, a deceptive technique where attackers use text messages to trick individuals into divulging sensitive information or clicking on malicious links, can have significant business impacts. Here are some key ways in which smishing can affect businesses:
Financial Loss:
Businesses can suffer financial losses if employees fall victim to smishing attacks that result in fraudulent transactions, unauthorized access to company accounts, or economic data theft.
Data Breaches:
Smishing attacks can lead to data breaches if employees unwittingly share sensitive company information through text messages. This can compromise customer data, intellectual property, or confidential business data.
Reputation Damage:
Falling prey to smishing can damage a business’s reputation. Customers, partners, and stakeholders may lose trust in the organization’s ability to protect their information, potentially losing business opportunities.
By raising awareness and enhancing defenses against smishing, businesses can better protect themselves from potential financial, reputational, and operational harm.
What to do if you become a Smishing victim?
Act quickly to minimize damage
- If you suspect you’ve fallen victim to a smishing attack, time is of the essence. Immediately contact your bank or credit card company to report unauthorized transactions and freeze your accounts.
- Change passwords for any compromised accounts, using strong, unique combinations for each. For an added layer of security, be sure to enable two-factor authentication where possible.
Report the incident
- File a report with your local law enforcement and the Federal Trade Commission (FTC).
- Provide them with as much detail as possible, including the phone number or short code used in the smishing attempt, the content of the message, and any actions you took in response. This information can help authorities track and prevent future attacks.
Monitor your accounts and credit.
- Keep a close eye on your financial statements and credit reports in the weeks and months following the incident.
- Look for any suspicious activity or unauthorized charges.
- Consider placing a fraud alert or credit freeze on your credit reports to prevent identity thieves from opening new accounts in your name.
How do I report Smishing?
Reporting smishing attacks is crucial to protect yourself and others from future scams. If you’ve encountered a suspicious text message, take immediate action to report it.
Report to your mobile carrier
Contact your mobile service provider’s fraud department. Most carriers have dedicated channels for reporting spam and phishing attempts. Provide them with the sender’s phone number and the content of the suspicious message.
Notify law enforcement
File a report with your local police department or the FBI’s Internet Crime Complaint Center (IC3). These agencies compile data on cyber crimes, which helps them identify trends and develop prevention strategies.
Alert consumer protection agencies
Submit a complaint to the Federal Trade Commission (FTC) through their website or consumer hotline. The FTC uses this information to investigate and shut down scammers. Additionally, consider reporting the incident to your state’s consumer protection office for localized support.
Remember, your vigilance in reporting smishing attempts contributes significantly to the broader effort of combating cyber fraud and protecting vulnerable individuals from falling victim to these scams.
How to Prevent Smishing?
To protect yourself from smishing attacks, remain vigilant and follow these best practices:
Be Skeptical of Unsolicited Messages
Always approach unexpected text messages with caution, especially those from unknown numbers. Legitimate organizations rarely request sensitive information via text. If a message claims to be from your bank or a government agency, verify it by contacting them directly through official channels.
Never Click on Suspicious Links
Avoid tapping on links in text messages, particularly if they’re from unfamiliar sources. These links may lead to phishing websites designed to steal your personal information. Instead, manually type website addresses into your browser or use official mobile apps.
Keep Your Software Updated
Regularly update your smartphone’s operating system and apps. These updates often include security patches that protect against the latest threats. Enable automatic updates whenever possible to ensure you’re always running the most secure versions.
Use Security Software
Install reputable mobile security software on your device. These apps can help detect and block suspicious messages, warn you about potentially malicious links, and provide an extra layer of protection against smishing attempts.
By staying alert and implementing these precautions, you can significantly reduce your risk of falling victim to smishing scams. Remember, legitimate organizations rarely request sensitive data via text message.
Do Not Reply or Provide Information
Resist the urge to reply to suspicious texts, even with “stop” or “remove.” Replying lets scammers know your number is active, and they may sell it to other spammers. Do not provide any personal or financial information in response to unsolicited texts.
Enable Fraud Alerts and Monitoring
Contact your bank, phone provider, and other accounts to enable fraud alerts and monitoring. This can notify you of suspicious activity and potentially block fraudulent transactions before harm is done.
Report Suspicious Texts
Forward any smishing texts you receive to 7726 (SPAM) to report them to your phone provider. You can also file an online report with the FTC at ftc.gov/complaint. Reporting helps build awareness and stop smishing schemes.
Be wary of urgent requests
Scammers often use a sense of urgency in their texts to trick victims into acting quickly before thinking critically. Take your time to verify any requests.
By staying alert and implementing these precautions, you can significantly reduce your risk of falling victim to smishing scams. Remember, legitimate organizations rarely request sensitive data via text message.
Major Smishing Incidents in Recent Years
Zimperium (2025)
According to mobile threat defense company Zimperium, SMS phishing attacks increased by 22% year over year, signaling a steady and concerning rise in mobile-targeted phishing attempts. This growth reflects a broader shift in attacker behavior, as threat actors increasingly target individuals through their smartphones, leveraging the immediacy and trust associated with SMS communications to deceive users into clicking malicious links or disclosing sensitive information.
Palo Alto Networks’ (2025)
Palo Alto Networks’ Unit 42 released a comprehensive analysis showing that more than 91,500 fake root domains were registered in early 2025, a large portion of which were tied to smishing and broader phishing campaigns. Alarmingly, over 26,300 of these domains were created in March alone, illustrating the industrial scale at which these operations are being executed. These domains are commonly used to host credential-stealing websites that impersonate legitimate brands, such as banks, delivery services, or government agencies.
UPS (2023)
UPS experienced a data breach where unauthorized access to their package lookup tool exposed some recipients’ details. UPS warned customers that attackers had targeted some recipients with smishing attacks demanding payment before delivery.
Verizon (2022)
Verizon acknowledged a smishing campaign targeting its users. The smishing text appeared to come from a user’s own phone number in hopes of them clicking the malicious link attached to the message.
State of Texas (2020)
A delivery notification smishing attack masquerading as DHL, FedEx, and Amazon became so widespread that Attorney General Ken Paxton sent a press release to warn Texas residents.
Apple iPhone 12 Scam (2020)
In September 2020, a smishing campaign surfaced to bait people into providing credit card info for a free iPhone 12. The scheme uses an order confirmation premise, in which the text message claims a package delivery has been sent to an incorrect address. The in-text URL link sends targets to a phishing tool posing as an Apple chatbot. The tool guides the victim through a process to claim their free iPhone 12 as part of an early access trial program but inevitably asks for credit card info to cover a small shipping fee.
To help protect yourself against a smishing attempt, learn the warning signs and smishing protection tips.
Conclusion
As smishing attacks continue to evolve, staying vigilant is crucial to protecting yourself and your sensitive information. By following the preventive measures outlined in this article, you can significantly reduce your risk of falling victim to these deceptive text message scams. Remember to always verify the sender, avoid clicking on suspicious links, and never share personal or financial details via text.
Keep your devices updated, use security software, and report any suspected smishing attempts to the proper authorities. With awareness and caution, you can navigate the digital landscape more safely and keep scammers at bay. Stay informed, stay alert, and stay protected against smishing threats.
FAQs
A phishing message often masquerades as a legitimate communication from a trusted source. It may claim to be from your bank, a government agency, or a popular service you use. These messages typically create a sense of urgency, asking you to “verify” account details, claim a prize, or address a security issue. Be wary of texts requesting personal information or containing suspicious links.
Clicking a link in a smishing text can lead to severe consequences. It may direct you to a fake website designed to steal your personal information or install malware on your device. This malware could compromise your data, track your keystrokes, or even give cybercriminals remote access to your phone.
To identify smishing, look for these red flags:
Unexpected messages from unfamiliar numbers
Urgent requests for personal information
Suspicious links or attachments
Poor grammar or spelling errors
Offers that seem too good to be true
Always verify the sender’s identity independently before taking any action. When in doubt, contact the purported sender directly using official channels.


No comments were posted yet