What Is a Hardware Wallet? A Complete Guide to Crypto Security

Bisma Farrukh
With the rapid growth of cryptocurrency adoption, security has become a top concern for investors. According to industry reports, over $3 billion in crypto was stolen through hacks and scams in 2022 alone, underscoring the importance of secure storage solutions. This is where hardware wallets come in.
A hardware wallet is considered one of the safest ways to store cryptocurrencies like Bitcoin, protecting your digital assets from hackers, malware, and online threats. In this guide, we’ll explore what a hardware wallet is, how it works, its benefits, and why it’s essential for crypto security.
Table of Contents
What Is a Hardware Wallet?
A crypto hardware wallet is a physical device that securely stores your cryptocurrency’s private keys offline. These private keys are essential for accessing and managing your digital assets, such as Bitcoin and other cryptocurrencies.
Unlike software wallets that connect to the internet, hardware wallets operate in an isolated, offline environment known as cold storage. This makes them highly resistant to hacking attempts, crypto malware, and phishing attacks.
Hardware wallets typically look like small USB devices and allow you to:
- Store cryptocurrency securely
- Send and receive digital assets
- Sign transactions without exposing private keys
How Does a Hardware Wallet Work?
A hardware wallet keeps your cryptocurrency private keys completely offline while still allowing you to securely send and receive digital assets. It ensures that sensitive information is never exposed to the internet.
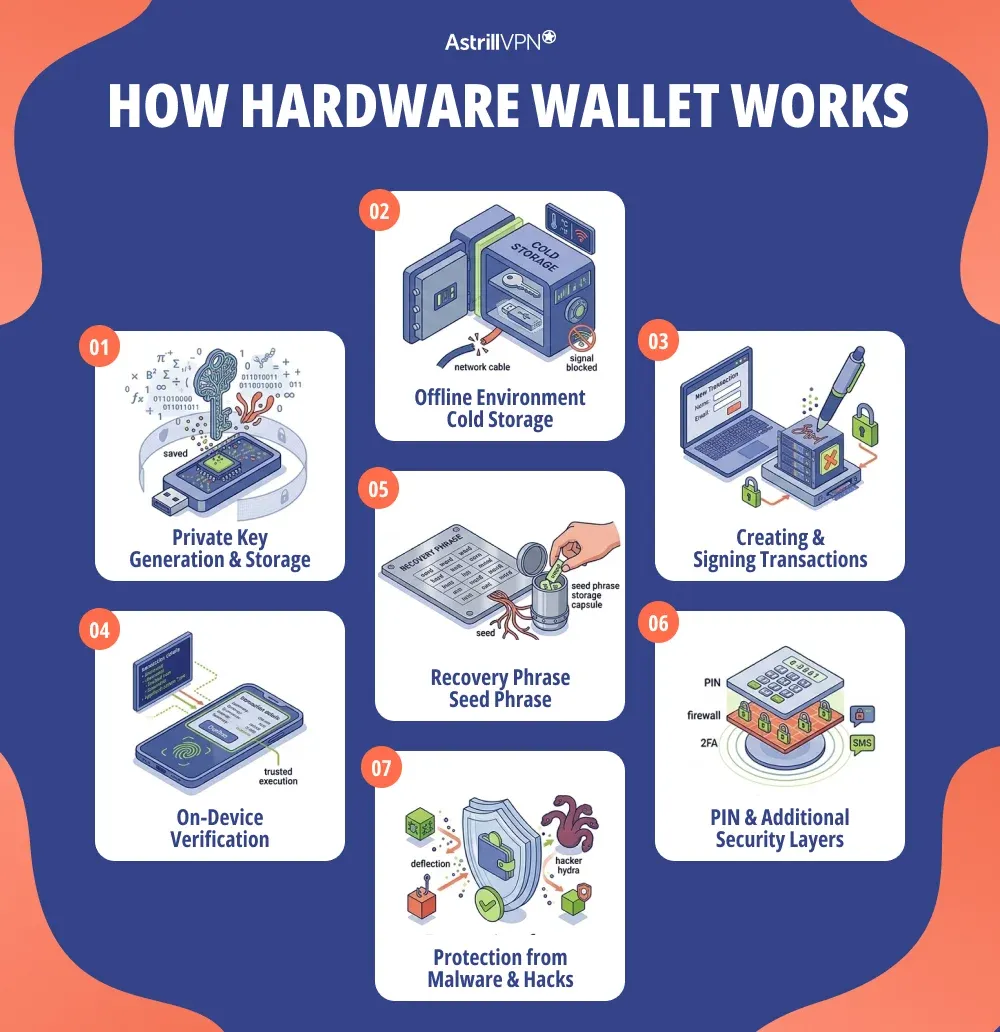
Private Key Generation and Storage
When you set up a hardware wallet, it generates a private key and a public key. The private key is stored securely inside the device and never leaves it, while the public key is used to receive funds. This offline storage is the foundation of its security.
Offline Environment (Cold Storage)
Hardware wallets operate in an isolated, offline environment known as cold storage. Even when connected to a computer or mobile device, the wallet ensures that private keys are never exposed online, protecting them from hackers and malware.
Creating and Signing Transactions
When you send cryptocurrency like Bitcoin, the process works like this:
- You initiate the transaction on your computer or mobile app
- The transaction is sent to the hardware wallet
- The wallet signs the transaction internally using your private key
- The signed transaction is then broadcast to the blockchain
On-Device Verification
Before completing any transaction, the hardware wallet displays the details on its screen. You must physically confirm the transaction, which prevents unauthorized transfers if your computer is compromised.
Recovery Phrase (Seed Phrase)
During setup, the wallet generates a 12–24-word recovery phrase. This phrase acts as a backup. If your device is lost or damaged, you can use it to restore your wallet and access your funds.
PIN and Additional Security Layers
Most hardware wallets require a PIN to unlock. Some also allow an extra passphrase, adding another layer of protection against unauthorized access.
Protection from Malware and Hacks
Because private keys never leave the device and all sensitive actions happen within it, malware on your computer cannot access your funds. This makes hardware wallets one of the safest ways to store cryptocurrency.
Key Statistics for Hardware Wallet
- Hardware wallets accounted for about 22% of all cryptocurrency wallets in 2026, indicating growing interest in cold storage solutions.
- Over 5.8 million hardware wallets had been shipped worldwide by the end of 2025, with sales rising about 31% in 2026 compared to 2025.
- Hardware wallet usage continues to grow: an estimated 56.6% of crypto users prefer self‑custody solutions, including hardware wallets, over custodial options.
- Despite this growth, only around 2–3% of global crypto users currently rely on hardware wallets as their primary storage, leaving large adoption potential.
- In user surveys, 61.5% of hardware wallet owners cited enhanced security as their main reason for using one.
- The hardware wallet market is expected to continue expanding rapidly, with a projected annual growth rate (CAGR) of 23–30% over the coming decade.
What Is a Hardware Wallet Used for in Crypto?
A hardware wallet plays a crucial role in managing and securing digital assets in the cryptocurrency ecosystem. It is not just a storage device; it’s a comprehensive security tool that gives users full control over their funds. Below are the main uses explained in detail:
Secure Storage of Cryptocurrencies
A hardware wallet is primarily used to store private keys offline, keeping your cryptocurrencies safe from online threats. Whether you hold Bitcoin or other digital assets, keeping them in a hardware wallet significantly reduces the risk of hacking, phishing, and malware attacks.
Safe Transaction Signing
Hardware wallets are used to securely sign cryptocurrency transactions. When you initiate a transaction, it is processed and signed by the device itself. This means your private keys are never exposed to your computer or the internet, adding a critical layer of protection.
Long-Term Crypto Storage
For investors who plan to hold crypto assets for an extended period, hardware wallets are ideal. They provide “cold storage,” meaning your funds remain offline and untouched, reducing their vulnerability to cyber threats and exchange-related risks.
Managing Multiple Cryptocurrencies
Most hardware wallets support a wide range of cryptocurrencies. This allows users to manage different assets from a single device without compromising security, making it convenient for diversified crypto portfolios.
Protection Against Exchange Failures
Many crypto users rely on exchanges to store their assets, but this comes with risks such as hacks or platform shutdowns. A hardware wallet removes this dependency by giving you full ownership and control of your funds.
Backup and Recovery of Funds
Hardware wallets generate a recovery phrase (seed phrase) during setup. This is used to restore your wallet and access your funds if the device is lost, stolen, or damaged. It ensures that your crypto assets are never permanently lost as long as the phrase is secure.
Enhanced User Control and Privacy
Using a hardware wallet means you retain complete control over your private keys and transactions. Unlike custodial services, no third party has access to your funds, which enhances both security and financial privacy.
Hardware Wallet Security
Hardware wallet security is one of the main reasons these devices are widely trusted for storing cryptocurrencies. By keeping sensitive data offline and adding multiple layers of protection, hardware wallets offer a strong defense against cyber threats.
Offline Storage Protection
The core security feature of a hardware wallet is offline (cold) storage. Private keys are generated and stored within the device, never being exposed to the internet. This significantly reduces the risk of hacking, phishing, and malware attacks.
Secure Element and Encryption
Many hardware wallets use a secure element chip, similar to those used in credit cards and passports. This chip is designed to store sensitive information safely and resist physical tampering. Combined with strong encryption, it ensures your private keys remain protected.
PIN Code Protection
Hardware wallets require a PIN to unlock. Multiple failed attempts can trigger security measures, such as temporary lockouts or device wipes, to prevent unauthorized access.
Passphrase Feature
Some wallets allow users to add an extra passphrase on top of the recovery phrase. This creates an additional hidden wallet, making it even harder for unauthorized users to access funds if they have the device.
On-Device Transaction Verification
Before approving any transaction, the hardware wallet displays the details on its screen. Users must manually confirm the transaction to ensure no transfers occur without physical approval.
Protection Against Malware
Even if your computer is infected with malware, a hardware wallet keeps your private keys safe. All critical operations take place within the device, so malicious software cannot access your funds.
Recovery Phrase Backup
During setup, a recovery (seed) phrase is generated. This allows you to restore your wallet if the device is lost, stolen, or damaged. Keeping this phrase secure is essential, as anyone with access to it can control your funds.
Protection from Supply Chain Attacks
Reputable hardware wallet manufacturers seal their devices and provide verification steps to ensure authenticity. Buying directly from official sources helps prevent tampered devices.
How to Use a Hardware Wallet?
The following process should be followed for using a hardware wallet.
1: Purchase a Trusted Device
Buy from official sources to avoid tampered devices.
2: Set Up the Wallet
- Connect the wallet to your device
- Install the required app
- Create a PIN
3: Save Your Recovery Phrase
Write down your seed phrase and store it securely offline.
4: Transfer Cryptocurrency
Send your crypto from an exchange wallet to your hardware wallet address.
5: Make Transactions
Use the wallet to send or receive crypto securely by confirming transactions on the device.
Hardware Wallet for Bitcoin
Hardware wallets are especially popular among Bitcoin users due to the asset’s high value. They provide a secure way to store Bitcoin without relying on third parties. By keeping your Bitcoin offline, hardware wallets protect against exchange hacks, phishing attacks, and unauthorized access.
If you hold a significant amount of Bitcoin or plan to invest for the long term, a hardware wallet is highly recommended. While small amounts can be stored in software wallets for convenience, hardware wallets provide unmatched security for larger holdings.
Benefits of a Hardware Wallet
Hardware wallets offer a wide range of advantages for cryptocurrency users, combining security, control, and convenience. Here are the key benefits:
Enhanced Security
The biggest advantage of a hardware wallet is the security it provides. By storing private keys offline, hardware wallets are highly resistant to hacking, malware, and phishing attacks. If your computer or mobile device is compromised, your funds remain safe.
Full Control Over Your Assets
Unlike custodial wallets or exchanges, a hardware wallet gives you complete ownership of your private keys. This means you have full control over your cryptocurrency and are not reliant on third parties for transactions.
Protection from Exchange Risks
Exchanges can be vulnerable to hacks, technical failures, or regulatory issues. Storing your crypto in a hardware wallet reduces reliance on third-party platforms and protects your assets from exchange-related risks.
Multi-Currency Support
Most hardware wallets support multiple cryptocurrencies, including Bitcoin, Ethereum, and many altcoins. This allows users to manage diverse portfolios from a single secure device.
Offline Transaction Signing
Hardware wallets allow transactions to be signed within the device itself. This means your private keys never leave the wallet, ensuring that every transaction is secure and tamper-proof.
Backup and Recovery
During setup, hardware wallets provide a recovery phrase (seed phrase) that can restore your wallet if the device is lost, stolen, or damaged. This ensures that your funds are never permanently lost as long as the recovery phrase is safely stored.
Convenience with Portability
Despite their robust security features, hardware wallets are portable and easy to use. They can connect to computers and mobile devices to manage and transfer funds without compromising security.
Long-Term Investment Storage
For investors planning to hold crypto assets for extended periods, hardware wallets are ideal for “cold storage.” Keeping funds offline reduces exposure to cyber threats and provides peace of mind.
Conclusion
As cryptocurrency adoption continues to grow, securing your digital assets is more important than ever. Hardware wallets offer a powerful solution by keeping your private keys offline and protected from cyber threats.
Whether you’re a beginner or a long-term investor, using a hardware wallet for storing Bitcoin and other cryptocurrencies significantly reduces your risk of loss due to hacks. By combining strong security features with ease of use, hardware wallets remain one of the most reliable tools for safeguarding your crypto investments.
FAQs
Here are some of the frequently asked questions.
A hardware wallet is used to securely store private keys offline and safely manage cryptocurrency transactions.
Yes, hardware wallets are considered one of the safest options for storing Bitcoin because they keep private keys offline and protected from cyber threats.
Hardware Wallet: Physical device, offline storage, highly secure
Software Wallet: App or program, connected to the internet, more convenient but less secure
While extremely secure, hardware wallets can be compromised if:
The recovery phrase is exposed
The device is tampered with before purchase
Users fall for phishing attacks
If you lose your device, you can recover your funds using your seed phrase on a new wallet. Without the seed phrase, you permanently lose access to your funds.


No comments were posted yet