Every breach begins with a single point of entry. It might be a phishing email that seemed completely legitimate. It could be a password reused across multiple accounts. Or it could be a plugin on a company website that hasn’t been updated in two years. Whatever the cause, attackers find it and exploit it.
These entry points have a name in cybersecurity: attack vectors. Understanding them isn’t the responsibility of security engineers alone. If you’re running a business, managing a team, or simply trying to protect your accounts, knowing how attacks start can help prevent them.
This guide covers everything from the basics to the most common attacker strategies and what you can do about each one.
Table of Contents
What Is an Attack Vector?
An attack vector is the means by which an attacker gains unauthorized access to a system. Simply put, it’s the “how” of a cyberattack, not the ‘what’ or the ‘why.’ When someone asks what an attack vector is, the easiest way to think of it is: it’s a door. It could be a fake login page that steals your password, a malicious email attachment, or an unpatched vulnerability in your server software. The attacker finds a door, figures out how to open it, and enters.
The variety of attack vectors is part of what makes defending against them truly challenging. There’s no single solution; each type of entry point requires its own defenses, which is why layered security matters more than any single tool.
Attack Vector vs. Attack Surface
These two terms get mixed up constantly, so let’s clear it up quickly. The attack surface is the entire collection of possible entry points in your environment, every app, every device, every employee account, every third-party integration. The attack vector is the specific technique used to exploit one of those entry points.
Think of your attack surface as a building with 40 possible ways in. The attack vector is the specific method a burglar uses to gain access to one of them. Reduce the number of doors and windows, and you shrink the attack surface. But you also need to make sure the remaining ones are actually secure; otherwise, reducing the surface doesn’t help much.
Attack Vector vs. Threat Vector
Threat vector is a slightly broader term. It can include behavioral patterns, environmental risk factors, or systemic vulnerabilities, not just the specific method of entry. But in everyday security conversations, the two are used interchangeably, and for the purposes of this guide, that’s fine. Both mean the pathway an attacker uses to get in.
Active vs. Passive Attack Vectors
Most attack vectors fall into one of two categories, and understanding the difference changes how you think about detection.
Active Attacks
Active attack vectors involve the attacker directly performing actions on your systems. Launching ransomware, flooding a server with traffic, and stealing credentials through a fake login page. These are the attacks that tend to cause obvious damage or trigger alerts. They’re loud, relatively speaking.
That doesn’t make them easy to stop. But at least they’re more likely to leave a trace and get caught.
Passive Attacks
Passive attacks are the quiet ones. The attacker isn’t breaking anything or stealing anything yet. They’re watching. Monitoring network traffic, mapping your systems, and collecting intelligence. The goal is to learn as much as possible before making a move.
This is what makes passive attacks so frustrating to deal with. Nothing seems wrong. No alerts go off. By the time you realize someone was snooping around, they’ve already gathered everything they needed to plan a much bigger attack.
The Most Common Attack Vectors in Cyber Security Today
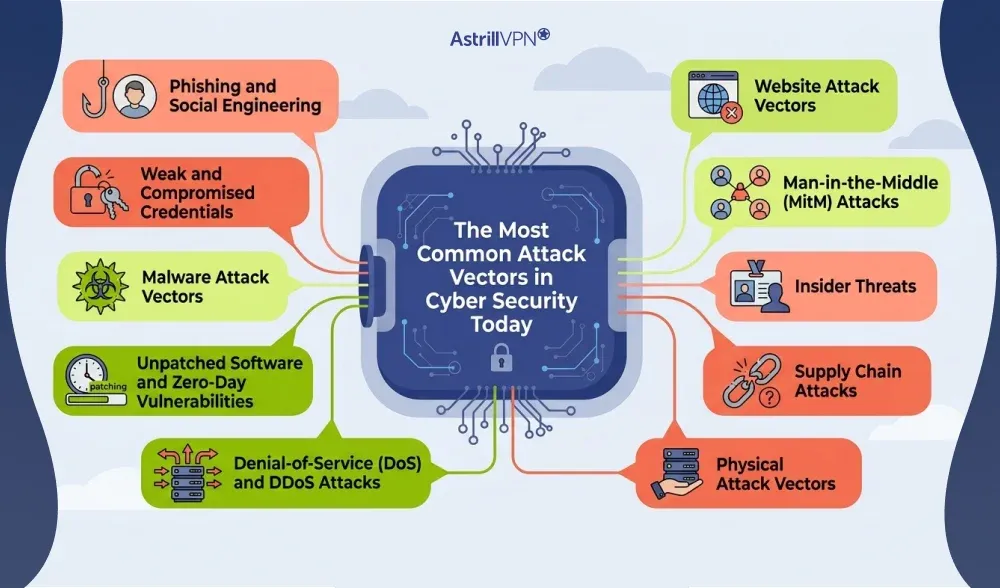
Here’s something that might surprise you: most attacks don’t use anything fancy. The most common attack vectors aren’t sophisticated zero-day exploits or cutting-edge AI tools. They’re the same basic techniques that have worked for years, because they still work. Organizations still leave passwords weak. People still click links they shouldn’t. Patches still sit unapplied for weeks.
Here’s what attackers are actually relying on.
1. Phishing and Social Engineering
Phishing has been the top initial attack vector globally for years, and it’s not going anywhere. The basic idea hasn’t changed: trick someone into thinking you’re trustworthy, then get them to click a link, open a file, or hand over their login credentials.
What has changed is how convincing it’s gotten. Modern phishing emails often look identical to legitimate ones. They know your name, your bank, your company. Spear phishing takes it further, targeting specific people with messages tailored to their LinkedIn profile, their email signature, or information from a previous breach.
And it’s not just email anymore. Smishing (SMS phishing) and vishing (voice calls) move the same scam to different channels. A call from “IT support” asking you to verify your credentials is just a phone phishing scam. Same playbook, different medium.
Social engineering is the bigger category here. It covers anything that exploits human psychology instead of technical vulnerabilities. Fear, urgency, authority, familiarity. These are the buttons attackers push to make people act before they think.
2. Weak and Compromised Credentials
Stolen or reused credentials are involved in the majority of breaches. Verizon’s 2025 Data Breach Investigations Report put the human element, which includes credential misuse, at over 74% of breaches. That stat should make everyone a little uncomfortable.
The core problem is password reuse. One account gets breached somewhere, the credentials end up on the dark web, and attackers run them through automated tools that test them across hundreds of services simultaneously. If your email password is the same as your banking password, that’s not really two separate accounts from a security standpoint.
Brute-force attacks and password spraying are also still common. Password spraying is particularly effective because attackers try a small number of common passwords against thousands of accounts, thereby avoiding triggering lockout policies that would catch repeated failed attempts on a single account.
Credentials can also be compromised through data breaches at third parties, malware that harvests saved passwords, or poorly secured password managers. Sometimes people do everything right and still end up exposed because a service they trusted got breached.
3. Malware Attack Vectors
Malware attack vectors are the methods used to deliver malicious software to a device or network. The delivery and the payload are two different things, but both matter when you’re trying to understand how an attack happened.
Common delivery methods include:
- Email attachments, especially macros in Office documents or disguised executables
- Malicious links that trigger silent downloads when clicked
- Infected USB drives or external storage left somewhere people will find them
- Fake software downloads or cracked apps distributed through unofficial channels
- Compromised packages in public code repositories
- Exploit kits embedded in otherwise normal-looking websites
Once it’s in, the malware can be anything. Ransomware that locks you out of your own files. Spyware that logs everything you type. Info-stealers that quietly copy saved passwords and send them to the attacker. Remote access trojans (RATs) that give attackers persistent, ongoing access to the system.
Info-stealers in particular have surged recently. Mandiant’s M-Trends 2025 report flagged their resurgence in 2024 as a direct driver of the rise in stolen credentials as an initial access method. The malware harvests credentials, which serve as the attack vector for the next stage.
4. Unpatched Software and Zero-Day Vulnerabilities
Every piece of software has bugs. The question is whether those bugs get fixed before someone figures out how to exploit them.
Unpatched software is one of the most avoidable attack vectors on this list, and also one of the most commonly exploited. Mandiant’s 2025 analysis found that vulnerability exploitation was the most common initial infection vector across all incidents they investigated, at 33% of cases. That’s a significant chunk of breaches that could have been prevented by a timely patch.
Zero-days are a different problem. These are vulnerabilities unknown to the vendor or not yet fixed, so there’s no patch available when attackers start exploiting them. State-sponsored groups are particularly known for stockpiling zero-days and deploying them against high-value targets. The 2024 Ivanti Connect Secure vulnerability (CVE-2024-21893) is a real example: remote code execution was achievable before most organizations had a chance to respond.
The organizations most at risk here are the ones with slow or chaotic patch management. When weeks pass between a patch becoming available and its actual deployment, that window stays wide open.
5. Website Attack Vectors
Websites are a big target, both the ones you build and the ones you visit. Website attack vectors cover a wide range of techniques aimed at exploiting how browsers and web applications work.
SQL injection has been around forever and is still actively used. An attacker inserts malicious SQL code into an input field, like a login form, tricking the database into running commands it shouldn’t. Depending on what’s accessible, this can mean full database exposure, account takeovers, or deleted records.
Cross-site scripting (XSS) is another persistent one. Attackers inject malicious scripts into a legitimate web page, which then execute in the browsers of anyone who visits. This can be used to steal session cookies, capture what users type into forms, or silently redirect them.
Cross-site request forgery (CSRF) is different. It abuses the fact that a logged-in user’s browser will automatically send their credentials with requests to a trusted site. An attacker tricks the user’s browser into making an unauthorized request on their behalf, with the site never knowing the difference.
Drive-by downloads are especially unpleasant because they don’t require the user to do anything except load the page. The malicious code runs automatically. For anyone building or maintaining a website, unvalidated user input, outdated plugins, and weak session handling are the weak spots that attackers most often target.
6. Man-in-the-Middle (MitM) Attacks
A man-in-the-middle attack puts the attacker between you and whoever you’re communicating with. They intercept the traffic, sometimes just reading it, sometimes altering it, while both sides of the conversation think they’re talking directly to each other.
Public Wi-Fi is the classic setup for this. When you connect to an open network at a coffee shop or airport, an attacker on the same network can intercept unencrypted traffic. If you’re not on HTTPS or a VPN, they can read what you’re sending or receiving.
This is one of the clearest practical use cases for a VPN. When you’re connected to AstrillVPN, your traffic is encrypted before it leaves your device. Even if someone on the same public network intercepts it, all they get is unreadable gibberish. It doesn’t fix every problem, but for this specific attack vector, encryption genuinely works.
MitM attacks occur through rogue access points (fake Wi-Fi networks set up to appear legitimate), SSL stripping (downgrading a connection from HTTPS to HTTP), and DNS spoofing (redirecting traffic to a fake version of a site). Detection is difficult because nothing looks obviously broken from the user’s side.
7. Insider Threats
Not every attack comes from outside. Insider threats involve people who already have legitimate access to your systems. That might be a disgruntled employee who decides to take data on their way out, or a contractor who’s been given more access than they actually need, or honestly just someone who made a mistake and clicked the wrong thing.
What makes insider threats particularly tricky is that the attacker is already inside the perimeter. They have valid credentials, logical reasons to be accessing certain systems, and often enough knowledge of internal processes to cover their tracks.
Mandiant’s 2025 report highlighted an interesting wrinkle here: a meaningful rise in insider threat cases tied to North Korean IT workers who got hired under false identities, then used their access for compromise and extortion. It’s a reminder that insider risk isn’t always about someone snapping and going rogue. Sometimes it’s a calculated, deliberate infiltration from the start.
8. Supply Chain Attacks
Supply chain attacks don’t go after you directly. They go after someone you trust, a software vendor, a managed service provider, a third-party integration, and use that relationship as a way in.
The logic is sound from an attacker’s perspective. If the target has strong defenses, find the weakest link in their ecosystem instead. A single compromised software update can plant a backdoor across thousands of organizations simultaneously. That’s exactly what happened with SolarWinds.
Third-party compromise was the second most common initial attack vector in 2025, accounting for around 15% of breaches and roughly doubling year over year. SolarWinds, Kaseya, and the Salesforce integration breach that affected Google Ads and dozens of other companies are all examples of how far the blast radius can spread from a single supply chain compromise.
9. Denial-of-Service (DoS) and DDoS Attacks
A denial-of-service attack isn’t usually about stealing data. The goal is to make something unavailable. Flood a server with enough traffic and it stops being able to respond to legitimate requests. DDoS (distributed denial-of-service) scales this up by using botnets, large networks of compromised machines, to send traffic from thousands of sources at once, which makes it much harder to block.
For businesses, even a few hours of downtime can mean significant revenue loss and reputational damage. For hospitals, utilities, or financial systems, the stakes are higher. DDoS attacks are also sometimes used as a smokescreen, keep the security team busy with the flood while a quieter intrusion happens somewhere else.
10. Physical Attack Vectors
Digital security gets most of the attention, but physical access is a real vector that often goes overlooked. An attacker who can get into your building can plug a malicious device into an exposed port, steal an unencrypted laptop, or simply sit near someone and watch them type their password.
USB drop attacks are a known technique where infected drives get left in parking lots or lobbies on purpose, banking on someone being curious enough to plug one in. It’s low-tech and it works. Lost or stolen devices are also a consistent source of exposure, especially when full-disk encryption isn’t in place.
Emerging Attack Vectors Worth Watching
The threat landscape shifts. Some attack vectors that were fringe a few years ago are now mainstream, and a few newer ones are gaining real traction.
AI-Powered Attacks
AI has genuinely changed the quality of attacks. Phishing emails generated by AI are harder to spot than the clunky, obviously fake ones from a few years back. They don’t have grammar issues. They know context. They sound like a real person wrote them.
Deepfake audio and video are being used for social engineering at a level that wasn’t really possible before. There have been documented cases of finance teams authorizing fraudulent transfers after receiving fake audio calls from someone impersonating a company executive. A 2024 survey found that 74% of IT leaders confirmed they’d experienced a breach that involved AI in some way.
IoT Vulnerabilities
Smart devices create a huge number of new entry points. Security cameras, thermostats, printers, medical devices, industrial sensors. They’re often built with minimal security, ship with default credentials that never get changed, and rarely get firmware updates.
Once an IoT device is compromised, it can serve as a foothold into the broader network or get conscripted into a botnet. The bigger problem is that most organizations don’t even have an accurate inventory of every connected device, which makes it nearly impossible to secure them consistently.
Cloud Misconfigurations
Cloud misconfigurations have quietly become one of the most common causes of large-scale data exposure. Publicly exposed S3 buckets, overly permissive access roles, unsecured APIs, and improperly set up identity controls. These aren’t exotic attack techniques. They’re configuration mistakes that leave data wide open.
Mandiant’s research found that cloud environments are most commonly compromised through phishing and stolen credentials, with weak identity controls being a consistent underlying factor. The cloud’s attack surface doesn’t exist in isolation from on-premises systems either. The connections between them create vulnerabilities of their own.
Server-Side Request Forgery (SSRF)
SSRF forces a server to make requests on behalf of the attacker, potentially granting them access to internal resources that should be completely off-limits to outsiders. It’s on OWASP’s Top 10 and has been appearing more frequently as organizations build more complex cloud- and API-based architectures.
Blind SSRF, where the attacker can’t directly see what the server returns but can still pivot to internal systems, is particularly hard to catch. The 2024 Ivanti breach involved SSRF techniques as attackers gained unauthorized access.
Attack Vector vs. Attack Surface: Why the Distinction Actually Matters
It’s easy to treat these as interchangeable, but they’re not, and conflating them leads to real gaps in security strategy.
Your attack surface is everything that could be targeted: web apps, open ports, employee email accounts, connected devices, third-party tools, and physical locations. It’s the total footprint.
Attack vectors are the specific techniques used to exploit any part of that surface. Even if you shrink your attack surface significantly, the parts that remain still need to be hardened against the specific vectors most likely to target them.
A startup with three employees and one web app has a much smaller attack surface than a large enterprise. But if that web app has SQL injection vulnerabilities and everyone’s using the same password, two of the most common attack vectors can still get an attacker all the way in. Size isn’t the same as security.
A good security strategy works on both: reducing the surface wherever possible, and specifically defending the remaining entry points against the vectors most relevant to your environment.
Where VPNs Fit Into Attack Vector Defense
A VPN isn’t a catch-all. Anyone telling it to you is overselling it. But for specific attack vectors, a good VPN provides real, practical protection.
Man-in-the-middle attacks on public networks become significantly harder when your traffic is encrypted before it leaves your device. An attacker sitting on the same network, intercepting packets, just gets encrypted data they can’t read. That’s a meaningful win for anyone who works remotely or travels frequently.
VPNs also mask your real IP address and location, which reduces the effectiveness of passive reconnaissance. If an attacker is mapping what they can learn about you from the outside, routing through a VPN server gives them a lot less to work with.
For teams with remote workers, VPNs create an encrypted channel back to the corporate network, which keeps internal traffic from being exposed over whatever internet connection someone happens to be using that day. AstrillVPN uses enterprise-grade encryption protocols that make this tunnel genuinely robust, not just technically present.
How to Actually Defend Against These Attack Vectors
No defense is bulletproof. But most attacks succeed because of gaps in fundamentals, not because the attacker was unbeatable. Fixing the fundamentals goes a long way.

Use Multi-Factor Authentication
MFA is the single highest-impact security change most organizations can make. It doesn’t matter how strong the password is if a stolen credential cannot log in without a second factor. Attackers who have valid, real passwords still get blocked. That’s a powerful defense against one of the most common attack vectors.
Password managers pair well with this. Unique, generated passwords for every account eliminate the problem of password reuse. A breach at one site doesn’t cascade into everything else. Make this a policy, not just a suggestion.
Patch Consistently and Quickly
Vulnerability exploitation is the most common initial infection vector in 2025 according to Mandiant. The fix is straightforward in principle, though less so in execution: know what’s running in your environment, prioritize patches by severity and exploitability, and verify they’re actually deployed.
For zero-days, the window between disclosure and exploitation can be hours, not days. Having a process for emergency patching and actually running it, is the difference between catching a breach early and finding out months later.
Train People on Phishing
Technology can only stop so much. Phishing works because it targets humans, and humans make mistakes. Regular, realistic training helps people recognize the warning signs, report suspicious emails, and pause before clicking things they shouldn’t.
Simulated phishing campaigns run internally are particularly useful because they produce real data. You find out who clicked, where the gaps are, and what training needs to be reinforced. Annual security awareness sessions aren’t enough anymore. The tactics evolve constantly.
Cut Down the Attack Surface
Disable what you’re not using. Close unnecessary ports. Remove software that serves no current purpose. Give users and applications only the access they actually need. Every extra entry point is another potential attack vector, and some of them are just sitting open for no reason.
For web applications specifically, input validation isn’t optional. SQL injection and XSS attacks exploit apps that trust user input without checking it first. This is a solved problem technically. It just needs consistent implementation.
Monitor and Log Everything
Even well-secured organizations get breached occasionally. What separates recoverable incidents from disasters is often the speed at which breaches are detected and contained. Good logging, intrusion detection, and endpoint monitoring all contribute to faster response.
Mandiant noted that a significant share of breaches lacked a determinable initial vector, largely because organizations lacked the logging needed to reconstruct what happened. Without logs, you can’t investigate. Without investigation, the same attack can happen again.
Treat Third-Party Access as a Risk
Assume that vendors and integrations are potential attack vectors, because they are. Vendor security assessments before onboarding, contractual security requirements, and ongoing monitoring of third-party access are all necessary parts of a mature security program.
Segment vendor access so that a compromise at one supplier doesn’t give attackers a straight path to your core systems. Don’t let trust substitute for verification.
Real-World Attack Vector Examples
Sometimes a real incident makes these concepts click better than any explanation.
SolarWinds
Attackers compromised SolarWinds’ build system and hid malicious code inside a legitimate software update for their Orion platform. Organizations that installed it, including government agencies and major corporations, unknowingly gave attackers a backdoor. The vector wasn’t a vulnerability in the targets’ own systems. It was trust in a software update from a vendor they had every reason to trust.
Credential Stuffing at Scale
After billions of credentials were exposed across various breaches, automated tools made testing them trivially easy. Attackers download a list of leaked credentials and run them against login portals across the internet. Organizations without MFA or anomalous login monitoring found accounts compromised without any phishing or malware involvement. Just a list of old passwords and a script.
Phishing to Ransomware
Most ransomware attacks begin with phishing. An employee receives what looks like a routine invoice, clicks the link, and downloads a file that installs a loader. The loader fetches and executes ransomware. The initial vector (phishing) enables the malware vector (the payload), which causes operational disruption across the whole organization. Each stage in the chain is a different vector, and interrupting any one of them stops the attack.
Quick Reference: Attack Vectors and Defenses
- Phishing and social engineering: Awareness training, email filtering, MFA
- Compromised credentials: MFA, password managers, credential monitoring, unique passwords per account
- Malware: Endpoint protection, email filtering, user training, application allowlisting
- Unpatched vulnerabilities: Timely patch management, vulnerability scanning, vendor advisory monitoring
- Website attack vectors: Input validation, web application firewall, secure coding, regular audits
- Man-in-the-middle attacks: VPN, HTTPS enforcement, avoiding unsecured public Wi-Fi
- Insider threats: Least privilege access, behavioral monitoring, access reviews, thorough offboarding
- Supply chain attacks: Vendor risk assessments, network segmentation, controlled third-party access
- DDoS attacks: DDoS mitigation services, rate limiting, network redundancy
- Physical attacks: Physical access controls, full-disk encryption, USB port restrictions
Wrapping Up
Attack vectors are the common thread running through almost every breach you’ll read about. The method changes from case to case, but the pattern doesn’t: attackers find an entry point, exploit it, and work from there. Phishing, stolen credentials, unpatched software, compromised vendors. These aren’t random. They’re the techniques that keep working because the same gaps keep existing.
Understanding attack vectors in cybersecurity doesn’t require a deep technical background. It requires recognizing that most attacks are opportunistic and that most successful ones exploit avoidable weaknesses. The defenses aren’t complicated in concept: authenticate properly, patch consistently, train your people, monitor what’s happening, and don’t trust third parties blindly.
Get those basics right and you’ve closed off the attack vectors that account for the overwhelming majority of real-world breaches. Start there.



No comments were posted yet