Blogs Posted by Arsalan
Eurosport is a premier destination for sports enthusiasts seeking comprehensive coverage of diverse and thrilling events. From the grueling stages of the Tour de France to the adrenaline-packed races of the UCI Mountain Bike World Series, Eurosport offers live access to many sports worldwide. However, Eurosport is a geo-restricted streaming service, meaning that it’s only […]
The 2026 FIFA World Cup is not just the usual tournament. This one is bigger than anything we have seen before. For the first time in history, 48 teams will compete across 104 matches in three host countries: the United States, Canada, and Mexico. Games run from June 11 through July 19, 2026, with the […]
VPNs have become essential tools for individuals and businesses looking to protect their data and access content without restrictions. However, when considering a VPN, one of the most common questions is: how much does a VPN cost? The price of a VPN can vary significantly depending on factors like features, service quality, and subscription duration. […]
Most people know what a VPN is. You install an app, hit connect, and your traffic routes through an encrypted tunnel. Simple, effective, and built for one device at a time. Now imagine you’re an IT administrator responsible for keeping 2,000 remote employees securely connected to a corporate network, from different cities, different devices, and […]
Encryption serves as a powerful tool to safeguard sensitive information from unauthorized access and maintain confidentiality. In this guide, we have explained VPN encryption in detail and discussed the types of protocols you may come across. So without further ado, let’s dive right into VPN encryption and understand what it is and what it is […]
VPNs are the best tool for protecting your online privacy and digital freedom. Nevertheless, many people debate about the legality of a VPN and how safe it is to use. It is legal and safe to use a VPN in most countries like the USA, the UK, Canada, Australia, etc. However, there are certain regions […]
The fantastic ability of Kodi to be customized as per users’ needs makes it popular among cord-cutters. Kodi users have to go through the lengthy process of downloading various Kodi skins to enhance their interface and add repositories to install an addon. Kodi builds have solved that issue perfectly. Rather than doing numerous things, a […]
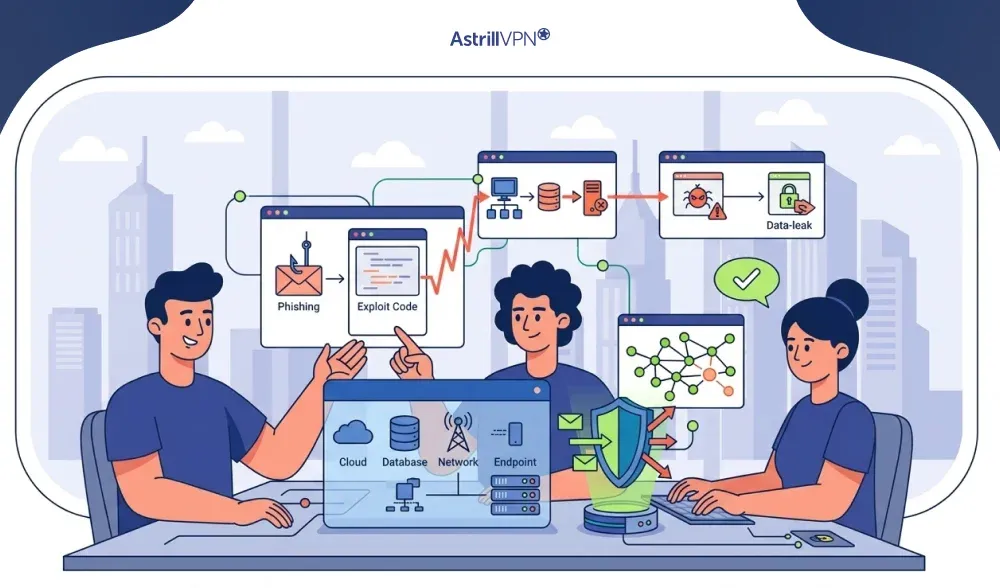
Every breach begins with a single point of entry. It might be a phishing email that seemed completely legitimate. It could be a password reused across multiple accounts. Or it could be a plugin on a company website that hasn’t been updated in two years. Whatever the cause, attackers find it and exploit it. These […]
Watching sports on a screen is a popular source of pleasure for enthusiasts worldwide. While stadiums have limited capacity, the fan base for most sports teams stretches far and wide. Traditionally, television was the go-to for live sports, but now, fans can watch games online via major streaming providers and free streaming sports sites. These […]
Poshmark has become one of the go-to destinations for secondhand fashion, and for good reason. The platform is convenient, the community is active, and the deals can be genuinely impressive. But any marketplace where strangers exchange money and goods attracts its share of bad actors, so the question of whether Poshmark is safe is one […]
Backdoors are one of the oldest and most persistent threats in cybersecurity. Backdoor attacks are not new, but they are growing. The data is sobering: Mandiant found backdoors in roughly 35% of malware families identified during incident response cases in 2024. Average breach costs involving backdoor access have climbed toward $4.7 million. And the average […]
Sky Sports holds the rights to Premier League football, Formula 1, cricket, golf, and more, but it is locked to UK viewers by default. If you are outside the UK, or simply want to get Sky Sports on your Firestick without paying for a full Sky TV package, the path is not immediately obvious. This […]
Here’s a scenario most VPN users have run into: you’re at home, VPN is on, and you try to log into your bank. Fraud alert. Or you open a local delivery app, and it thinks you’re in some city three time zones away. Nothing has gone wrong, technically. Your VPN is doing exactly what it’s […]
Virtual Private Networks (VPNs) have become an essential tool for protecting online privacy, securing remote work connections, and bypassing network restrictions. When using a VPN behind certain routers or firewalls, users may encounter connectivity issues. This is where VPN passthrough becomes important. VPN passthrough is a networking feature that allows VPN traffic to pass through […]
The conversation around network security has shifted. SASE keeps entering the frame, often positioned as the future of enterprise access, while VPNs quietly continue doing what they’ve always done. So what actually separates the two, and does one make the other obsolete? The short answer is no. They solve different problems for different audiences. Here’s […]
What 2,000 Users and Millions of VPN Sessions Reveal About Modern Cyber Habits Survey cohort: 2,000 respondents across the United States, United Kingdom, Germany, India, and the United Arab Emirates. Session dataset: aggregated, anonymized telemetry from millions of active VPN connections. All findings reported in accordance with responsible disclosure and data minimization principles. SECTION 01 […]
Shein has gained a massive global following with its trendy and affordable apparel. However, concerns about data security, product quality, and ethical practices have led many people to question the safety of shopping on this platform. In this comprehensive guide, we will explore Shein’s security measures, past data breaches, and steps you can take to […]
Transmission Control Protocol and User Datagram Protocol are two types of network protocols that can be used in file sharing. You can choose whether you want TCP or UDP for VPN when setting up routers or configuring firewalls. In order to choose which protocol is best for you, you must properly understand the difference between […]
The 2025/26 season marks the 71st edition of Europe’s premier club football tournament and the 34th year since it adopted the name UEFA Champions League. The competition begins on July 8, 2025, and will culminate with the final in Budapest, Hungary, on Saturday, May 30, 2026. The Champions League isn’t just a European tournament, it’s […]
Most people assume they are covered the moment they click “New Incognito Window” or install a free ad blocker from the Chrome store. The truth is a lot more layered than that. VPNs, Incognito Mode, and ad blockers each protect you from a different slice of the problem, and none of them covers the whole […]
A script kiddie hacker is someone who performs hacking activities using tools, exploit kits, or automated attack software created by others. Instead of discovering vulnerabilities or building their own attack methods, they rely on publicly available scripts to scan targets, attempt logins, exploit known weaknesses, or disrupt services. The difference between a generic script kiddie […]
While many people are familiar with the concept of a VPN, few truly understand the concept of how it works. VPNs were originally designed to enable secure data sharing, but the technical jargon often makes the details seem complex and intimidating. One term frequently encountered in discussions about VPNs is the “VPN tunnel” or “encrypted […]
Astrill VPN is an excellent, foolproof, and hackproof protection tool for your online privacy and anonymity on your personal computer. It keeps all your sensitive data encrypted and permits you to access content from anywhere. Follow this guide thoroughly to learn how to setup AstrillVPN on Windows and get started: How to Setup AstrillVPN – […]
Internet service providers (ISPs) can limit our bandwidth or reduce our internet speeds, also known as internet throttling, for various reasons such as network congestion, data caps, and even to discourage certain types of internet activities like streaming and gaming. Internet throttling can significantly affect internet users who rely on high-speed internet for online gaming, […]
Social media has become an integral part of our daily lives, serving as a platform for our hobbies, entertainment, and even career growth as influencers. But bеwarе! The drеadful Instagram IP ban can dеstroy it all. No account accеss, zеro activity, and your businеss scrееchеs to a halt. But don’t panic, my friеnd! Wе’vе got […]
Virtual Private Networks (VPNs) enhance online privacy and security by masking users’ IP addresses and encrypting their internet traffic. However, the question arises: Can VPN traffic be traced back to the user? This inquiry delves into VPN providers’ capabilities, potential vulnerabilities, and the importance of understanding the limitations of VPN anonymity. Let’s explore the intricacies […]
Every time you open a website, send a message, or log in to an account, your data travels across multiple networks before reaching its destination. Most of the time, that journey is invisible and secure. But when an attacker quietly inserts themselves into that path, the risks change fast. On-path attacks are one of the […]
Mac systems include built-in security protections, but they are not immune to malware. Threats targeting macOS have increased steadily, with attackers distributing adware, spyware, credential stealers, and remote access tools designed specifically for Apple devices. These threats often operate quietly, making detection difficult without deliberate checks. Knowing how to check for malware on Mac is […]
When you use a website, start a video call, or connect to a secure service, your data travels through various networks owned by internet providers, cloud services, governments, and businesses. BGP is the routing system that directs this data. BGP operates in the background, making rapid decisions about data paths. When it functions well, the […]
The World Series is one of the most anticipated sporting events in the United States, bringing together the American League’s and National League’s champions for a thrilling baseball finale. In 2026, millions of fans across the globe will tune in to watch the drama unfold. Whether you’re a die-hard baseball enthusiast or a casual viewer, […]
The Premier League is one of the most popular and widely viewed football leagues globally. Its appeal extends far beyond the UK, attracting a massive international audience. The Premier League’s combination of top-tier talent, competitive balance, and a rich history of dramatic matches makes it captivating. Whether it’s iconic rivalries or world-class players competing at […]
The Rose Bowl, often called the “Granddaddy of Them All,” is one of the most prestigious college football bowl games in the United States. Scheduled for January 1, 2026, this event will feature top-tier college football teams and capture fans worldwide. Here’s a comprehensive guide on streaming the Rose Bowl live, ensuring you don’t miss […]
Internet security is no longer a concern limited to large organizations or tech professionals. Every time you connect to the internet, your data travels through multiple networks, servers, and systems that you do not control. This is where VPN security becomes essential. A Virtual Private Network, or VPN, is designed to protect your online activity […]
Are you ready to dive into the thrilling world of NFL games without ever leaving your home? Whether you’re a die-hard football fan or just looking to catch the big games, watching the NFL live online has always been challenging. This comprehensive guide explores the best ways to stream NFL games live on your devices, […]
In today’s digital age, where nearly every aspect of our personal and professional lives is connected to the internet, cybersecurity threats have become more sophisticated and dangerous. Ransomware stands out as one of the most disruptive and costly. Whether it’s a multinational corporation, a local hospital, or an individual user, no one is immune to […]
If you’ve recently encountered a message on your iPhone asking you to wait an hour before changing a password or other security setting, you’re not alone. This is Apple’s security delay feature, and it’s designed to protect your device from sophisticated theft tactics. In this comprehensive guide, we’ll walk you through everything you need to […]
A cyberattack occurs every 39 seconds, totaling over 2,200 attacks daily. Website owners face constant threats from hackers, and a single breach can cost thousands of dollars, erode customer trust, and significantly impact search rankings. This guide covers everything you need to protect your website: the vulnerabilities hackers exploit, the most dangerous current threats, and […]
A UDP flood attack is a type of Distributed Denial-of-Service (DDoS) attack that exploits the connectionless nature of the User Datagram Protocol (UDP) to overwhelm a target system, server, or network. By sending a high volume of UDP packets to random or specific ports, attackers consume bandwidth and system resources, causing slowdowns or complete service […]
Transport Layer Security, or TLS, is a protocol designed to secure digital communications. It ensures that data exchanged between a user and a server remains private, authenticated, and protected from tampering. Through TLS encryption, sensitive information such as passwords, messages, and financial details cannot be intercepted or read by unauthorized parties. TLS security relies on […]
Most people think of stolen passwords or hacked servers when they hear about online security. But even something as simple as a domain name can decide if your business stays online or vanishes overnight. It might sound dramatic, but losing your domain can cause chaos. One minute, everything works. Next, your website redirects to a […]
When your browser says your connection is not private, it means it can’t confirm a secure link between your device and the website. This warning appears if security details are missing or unreliable, preventing the page from loading until you choose an action. Browsers do this to protect your data, since online security is now […]
When organizations review DDoS attack examples, they examine the events that have caused widespread outages, financial losses, and reputational damage. These cases help security teams understand how large DDoS attacks are constructed, how quickly they can escalate, and why each new wave often surpasses the one before it. The DDOS attacks force businesses to reassess […]
Spam bots are automated programs designed to flood online platforms with unwanted messages, fake accounts, or malicious links. Unlike useful bots that help with search engines or customer support, spam bots exist to exploit digital spaces for profit, disruption, or manipulation. They can target email inboxes, comment sections, social media feeds, and websites, often leaving […]
The season of discounts and deals is finally here as Black Friday is just around the corner. To make this season much more amazing, AstrillVPN is offering the best and biggest Black Friday VPN deal. Overview Get 27 months of premium VPN protection for just $199 and that’s only $7.37 per month. This Black Friday offer includes: Compared […]
Secondhand shopping apps like Depop feel exciting because you can find rare vintage pieces, boost your income by reselling, or simply browse for something unique. At the same time, the risk of scams has grown. According to a consumer survey, 57 percent of Depop buyers reported being scammed over the past two years. Another report […]
Spam calls are one of the most frustrating parts of modern communication. Whether it is a fake investment opportunity or a fraudulent tech support offer, these calls are designed to trick you into trusting the person on the other end. One of the most common tricks scammers use is making their number look local. You […]
Worm malware is one of the oldest and most stubborn threats in the cybersecurity world. Unlike other harmful software that requires users to click or download something, worms are sneaky. They can copy themselves and hop from one computer to another, usually without anyone noticing. One worm can overload networks, mess up services, and put […]
One of the simplest ways someone can track you is through your IP address. It is your virtual address in numerical format. Your IP address contains your location information, and anyone can track where you are located through your IP address. Changing your IP address is the best way to protect yourself from cyber threats. […]
Unlike regular phishing, which targets random users, and spear phishing, which focuses on specific individuals, whaling phishing targets top executives, such as CEOs and CFOs. These attacks are highly personalized and often appear as legitimate internal communications, making them much more challenging to detect. Recent data shows that whaling incidents are increasing in frequency and […]
Cybersecurity researchers have identified a significant rise in NFC relay malware targeting European payment cards through Android devices. Over 760 malicious apps have been discovered in recent months using this technique to steal financial information. Unlike traditional banking trojans, which rely on overlays or remote access tools to capture credentials, NFC malware exploits Android’s Host […]























![Can VPN Be Traced in 2026? [Updated]](https://www.astrill.com/blog/wp-content/uploads/2022/06/can-vpn-be-traced.jpg)