Cross-Site Request Forgery (CSRF): What It Is, and How to Prevent It?

Bisma Farrukh

In today’s web-driven world, security threats are constantly evolving, and one of the most overlooked yet dangerous is Cross-Site Request Forgery. Unlike obvious hacking attempts, CSRF quietly exploits a user’s trusted session to perform unauthorized actions without their knowledge. Whether it’s transferring funds, changing account details, and submitting forms, these attacks can have serious consequences. Understanding what CSRF is, how it works, and how to prevent it is essential for both developers and everyday users.
Table of Contents
What Is CSRF?
Cross-Site Request Forgery is a type of web security vulnerability where an attacker tricks a user into performing actions on a website where they are already authenticated. Because the browser automatically includes session credentials, the website assumes the request is legitimate, even though the user never intended it.
What Is a CSRF Attack?
A CSRF attack occurs when a malicious actor forces an authenticated user to send a request to a web application without their consent. The attack works because the website trusts the user’s browser session. This request could perform sensitive actions such as:
- Changing account passwords
- Transferring money
- Updating email addresses
- Making purchases
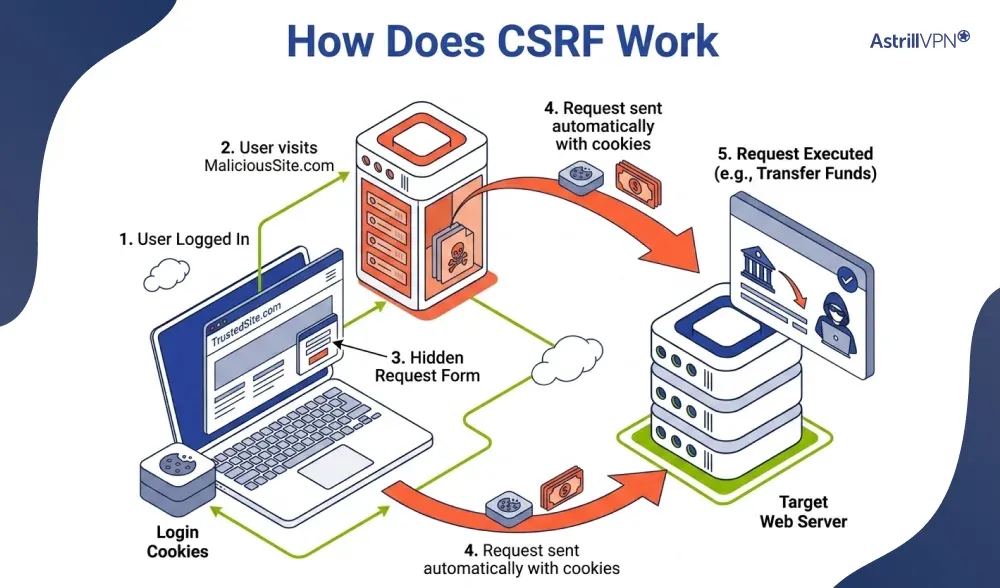
How Does CSRF Work?
Here’s a step-by-step breakdown of how a CSRF attack typically works:
- A user logs in to a trusted website, such as an online banking site.
- The website authenticates the user and stores a session cookie in the browser.
- The user visits a malicious website and clicks a crafted link.
- The malicious site sends a hidden request to the trusted website.
- The browser automatically includes the user’s session cookie.
- The trusted website processes the request if it came from the user.
CSRF Vulnerability
Websites that fail to validate the origin of requests are especially at risk. A CSRF vulnerability exists when a web application:
- Relies only on session cookies for authentication
- Does not verify whether the request is intentional
- Lacks anti-CSRF protections such as tokens
Cross-Site Request Forgery Example
Imagine you’re logged into your bank account. While browsing another site, you unknowingly click a malicious link containing this hidden request:
Because your browser is still authenticated, the bank processes the request and transfers money without your approval.
Common CSRF Attack Examples
Some real-world inspired scenarios include:
- Changing a user’s email address to the attacker’s email address
- Submitting unauthorized form requests
- Triggering password resets
- Making purchases on e-commerce platforms
- Social media actions like posting and liking content
What Is CSRF Protection?
CSRF protection is a security measure that prevents unauthorized requests from being executed. These protections ensure that every request is legitimate and intentionally made by the user. CSRF protection ensures that every sensitive request made to a web application is legitimate and intentional. Since browsers automatically include cookies, such as login sessions, with requests, attackers try to exploit this behavior. CSRF protection stops this by verifying the origin and authenticity of each request.
Common CSRF Protection Methods
These are some of the common CSRF Protection methods.
1. CSRF Tokens (Anti-CSRF Tokens)
A unique, secret token is generated by the server and included in forms and requests. When the request is submitted, the server checks if the token matches. If it doesn’t, the request is rejected.
2. SameSite Cookies
Cookies can be configured with a “SameSite” attribute to prevent them from being sent with cross-site requests, reducing the risk of unauthorized actions.
3. Origin and Referer Validation
The server checks the request headers (Referer) to confirm the request is coming from a trusted source.
4. Double Submit Cookies
This method sends a token in both a cookie and a request parameter. The server verifies that both values match before processing the request.
Key CSRF Attack Statistics
Here are key CSRF attack statistics:
- Around 1 in 3 web applications still contain CSRF vulnerabilities, although this has improved from 1 in 2 in previous years.
- CSRF accounts for roughly 15% of all web application attacks, making it a significant but overlooked threat.
- Industry data shows that over 30% of CMS platforms lack adequate CSRF protection, leaving them vulnerable to exploitation.
- Between 2023 and 2025, CSRF-related website defacement incidents increased from 20% to 35%, indicating a rising trend in real-world attacks.
- In cybersecurity datasets, CSRF vulnerabilities account for about 0.29% of all recorded vulnerabilities. They affect over 1.3% of tested websites, highlighting their targeted nature.
- CSRF-related breaches in the financial sector increased by around 12%, underscoring the heightened risk in sensitive industries.
- Cyberattacks (including CSRF and other attacks) affect tens of thousands of websites daily, underscoring the scale of web security threats.
CSRF Token: The Key Defense Mechanism
What Is a CSRF Token?
A CSRF token is tied to a user’s session and embedded in forms and requests. When the user submits a request, the server verifies the token against the expected value. If it doesn’t match, the request is rejected.
How a CSRF Token Works?
- When a user logs in, the server generates a random token.
- The token is included in web forms and API requests.
- When the form is submitted, the token is sent back to the server.
- The server compares it with the stored token.
- If valid → request is processed; if not → blocked.
CSRF Prevention Techniques
These are some of the best CSRF prevention techniques.
CSRF Tokens (Anti-CSRF Tokens)
One of the most effective ways to prevent Cross-Site Request Forgery (CSRF) attacks is to use CSRF tokens. These are unique, unpredictable values generated by the server and tied to a user’s session. The token is embedded in forms and included in API requests, and the server validates it upon submission. Since attackers cannot access and guess this token, any forged request without a valid token is automatically rejected.
SameSite Cookie Attribute
The SameSite attribute helps protect against CSRF by controlling how cookies are sent with cross-site requests. When set to “Strict” or “Lax,” the browser prevents cookies from being sent with requests from external websites. This prevents attackers from exploiting a user’s authenticated session, as the necessary cookies won’t be sent along with malicious requests.
Origin and Referer Header Validation
Web servers can check the Origin and Referer headers of incoming requests to verify the source of the request. If a request originates from an untrusted domain, it can be blocked. This technique adds a layer of security by ensuring that only requests from legitimate sources are processed, reducing the chances of unauthorized actions.
Double Submit Cookie Technique
In this method, a CSRF token is stored in a cookie and sent with the request. The server then compares the two values to ensure they match. If they don’t, the request is denied. This approach works well in stateless applications where server-side session storage may not be used.
Custom Request Headers (for APIs)
In modern web applications and APIs, CSRF protection can be implemented using custom headers, such as X-CSRF-Token. Browsers do not allow cross-origin sites to send custom headers without permission, which makes it harder for attackers to forge such requests. This technique is commonly used in AJAX-based applications.
User Authentication and Re-Authentication
Requiring users to re-authenticate before performing sensitive actions such as changing passwords and making financial transactions adds an extra layer of protection. If a CSRF attack attempt occurs, the attacker cannot proceed without the user’s credentials, making the attack ineffective.
Limiting Session Lifetime
Reducing the duration of user sessions minimizes the window of opportunity for attackers. If a session expires quickly, even if a user unknowingly visits a malicious site, the chances of a successful CSRF attack are significantly reduced.
CAPTCHA and User Interaction Checks
Adding CAPTCHA and requiring user interaction can help distinguish genuine users from malicious requests. This ensures that sensitive actions are performed intentionally rather than triggered silently by an attacker.
Conclusion
Cross-Site Request Forgery is a silent but powerful web security threat that exploits user trust and authenticated sessions. While it may not always be visible, its impact can be severe, especially for financial and sensitive platforms. The good news is that with proper safeguards like CSRF tokens, secure cookies, and request validation, these attacks can be effectively prevented. For developers, implementing strong defenses is essential, and for users, staying cautious while browsing can make all the difference.
FAQs
Here are some of the most frequently asked questions.
A CSRF token is a unique security value used to verify that a request is genuine. It is important because it prevents attackers from forging requests on behalf of authenticated users.
Common examples include unauthorized fund transfers, changing account details, submitting forms, and performing actions on social media without user consent.
Websites that rely heavily on cookies for authentication and lack proper request validation, such as banking, e-commerce, and social media platforms, are most vulnerable.
CSRF tricks users into making unintended requests.
XSS (Cross-Site Scripting) injects malicious scripts into a website to steal data and manipulate content.
CSRF attacks typically perform actions rather than directly stealing data. However, they can indirectly lead to data exposure by changing account settings and enabling further attacks.


No comments were posted yet