Identity-Based Attacks: Types, Examples, and Prevention tips

Bisma Farrukh

As organizations increasingly rely on cloud services, remote work, and digital identities, cybercriminals are shifting their tactics. Instead of breaking into systems using malicious software, attackers are now targeting user identities like credentials, authentication systems, and access privileges. These threats, known as identity-based attacks, are harder to detect because they often appear as legitimate user activity. Understanding how these attacks work is essential for individuals and businesses looking to strengthen their cybersecurity posture in 2026.
Table of Contents
What Are Identity-Based Attacks?
Identity-based attacks are cyberattacks where attackers exploit user credentials, authentication mechanisms, and identity systems to gain unauthorized access to networks, applications, and data. Rather than relying on traditional malware, these attacks use stolen and compromised login details to impersonate legitimate users. Once inside, attackers can move freely within a system, often without triggering security alerts. This makes identity-based attacks particularly dangerous, as they blend in with normal user behavior and bypass many conventional defenses.
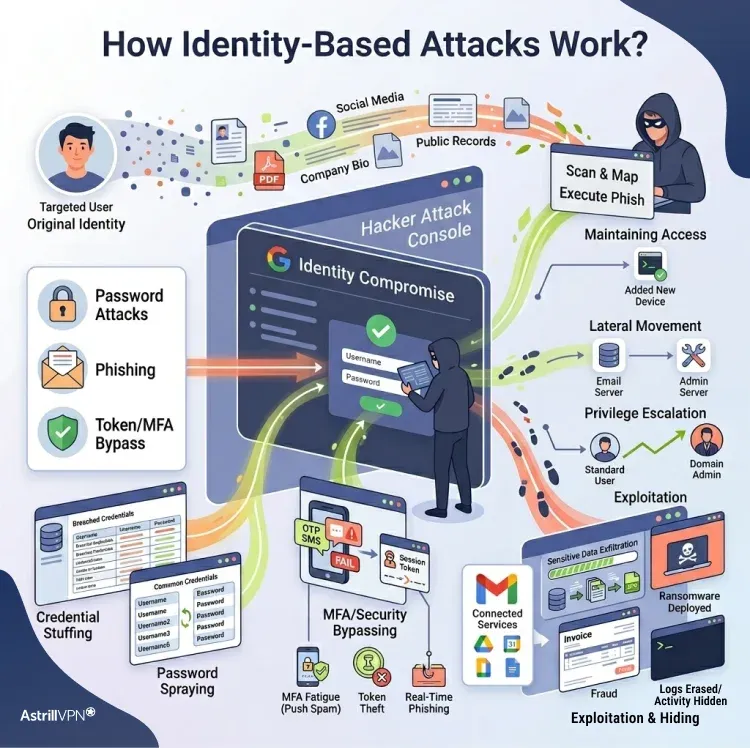
How Identity-Based Attacks Work?
- Attackers first choose their target, which can be an individual user, employee, or entire organization. They often collect information from public sources such as social media, data leaks, and company websites to identify usernames, email formats, and access systems.
- Attackers try to obtain login credentials using methods such as phishing emails, fake login pages, credential stuffing from leaked databases, password spraying, and social engineering. The goal is to steal valid usernames and passwords and trick users into revealing them.
- Once attackers obtain valid credentials, they log in to the system as legitimate users. Since they are using real identity information, their logins often appear normal and do not trigger security alerts.
- Attackers attempt to bypass additional security layers, such as multi-factor authentication (MFA), using techniques such as MFA fatigue attacks, session token theft, and real-time phishing that captures OTP codes.
- After gaining entry, attackers try to maintain long-term access by changing recovery emails, adding new authentication devices, and stealing session tokens so they don’t need to log in again.
- Attackers move across systems using the compromised identity to access emails, databases, shared drives, and admin tools. Because they appear as a trusted user, their activity often goes unnoticed.
- If the compromised account has limited access, attackers try to gain higher privileges. They exploit weak permissions and additional vulnerabilities to gain admin-level access and full system control.
- At this stage, attackers steal sensitive data, deploy ransomware, conduct fraud, and launch further attacks. This is usually the most damaging phase of the attack.
- Attackers may delete logs, hide activity, and use encrypted communication channels to avoid detection and prolong access before being discovered.
Why Are Identity-Based Attacks Important?
Identity-based attacks are important because they are the most common and effective way for cybercriminals to breach systems. Instead of using malware or exploiting software vulnerabilities, attackers now focus on stealing user identities such as usernames, passwords, and authentication tokens to gain access. This makes them especially dangerous because the attacker appears to be a legitimate user, allowing them to bypass many traditional security tools such as firewalls and antivirus systems.
Studies show that over 80% of data breaches in 2025–2026 involved compromised identities, highlighting the centrality of identity in modern cyberattacks. These attacks are also critical because a single stolen account can give access to emails, cloud storage, financial systems, and internal networks, enabling attackers to move deeper into systems and cause widespread damage.
Emerging Threats in Identity Security
Identity security is evolving faster than traditional cybersecurity controls. Instead of breaking into systems, attackers are now focusing on stealing, faking, and manipulating identities. As organizations adopt cloud systems, AI tools, and remote access, new identity threats are emerging that are more automated, scalable, and harder to detect.
1. AI-Powered Phishing and Social Engineering
One of the fastest-growing threats is the use of artificial intelligence to create highly convincing phishing attacks. Attackers now use AI to generate realistic emails, fake login pages, and even deepfake voice calls that impersonate executives and IT staff. These messages are personalized using leaked data from social media and corporate profiles, making them extremely difficult to detect. In 2025–2026, AI-driven attacks became the #1 identity security concern for most organizations, with over 87% reporting exposure to deepfake and AI-based identity threats.
2. MFA Bypass Attacks (Beyond OTP Security)
Multi-factor authentication (MFA), once considered highly secure, is now being actively bypassed. Attackers use techniques like MFA fatigue (push bombing), adversary-in-the-middle phishing, and session token theft to gain access even after login approval. Instead of breaking encryption, they manipulate users into approving access or steal active sessions after authentication.
3. Token Theft and Session Hijacking
Instead of stealing passwords, attackers increasingly target authentication tokens and active sessions. Once a session cookie or token is stolen, attackers can directly access accounts without triggering login alerts and MFA prompts. This makes detection extremely difficult because the attacker appears to be a legitimate, logged-in user. Security research indicates that more than 60% of modern identity-based attacks involve tokens, sessions, and credential reuse rather than direct password theft.
4. Non-Human Identity (NHI) Attacks
A new and rapidly growing threat involves non-human identities such as APIs, service accounts, AI agents, and automated bots. These identities often have persistent access and are not monitored as closely as human users. Attackers exploit weakly secured API keys and over-permissioned service accounts to gain long-term access. Recent 2026 reports highlight that organizations are struggling to control the explosion of non-human identity usage in cloud environments, significantly increasing attack surfaces.
5. Deepfake-Based Identity Impersonation
Deepfake technology is now being used to impersonate executives, employees, and customers in real time. Attackers use AI-generated voices and videos to trick help desks and finance teams into resetting credentials and approving fraudulent transactions. These attacks rely on psychological trust rather than technical exploits. Around 74% of identity-related incidents in late 2025 involved some form of impersonation or behavioral manipulation.
6. Helpdesk and Support System Exploitation
Instead of attacking systems directly, hackers now target IT support teams. They impersonate employees and request password resets, MFA device changes, and account recovery. Once the helpdesk approves the request, attackers gain legitimate access to internal systems. Recent cybersecurity findings show that a large portion of enterprise breaches now begin with identity manipulation via IT support channels.
7. Passkey and Passwordless Transition Challenges
While passkeys and passwordless authentication are improving security, attackers are already adapting. New research shows that even passkey systems can be targeted through infected devices, browser manipulation, and phishing relay attacks. This means no authentication method is fully immune if the endpoint is compromised. Academic studies confirm that while passkeys are significantly more resistant to phishing, advanced attack vectors still exist in high-resource threat scenarios.
Identity-based Attacks: Real-world examples
Some notable examples of identity-based attacks are mentioned below.
1. Change Healthcare Attack (2024): MFA Bypass + Identity Compromise
One of the largest healthcare cyberattacks in history occurred in 2024, when attackers gained access through an unprotected system and weak identity controls. The system lacked proper multi-factor authentication on a critical server, allowing attackers to enter and disrupt operations across the U.S. healthcare network.
The attack caused massive disruption in billing systems and exposed sensitive patient data. It became a textbook example of how identity weaknesses can shut down essential infrastructure. The breach impacted 192.7 million patient records, making it one of the largest healthcare data breaches ever recorded.
2. Microsoft 365 / SaaS Identity Phishing Campaign (2024–2025)
A long-running phishing campaign targeted Microsoft-based identity systems (including ADFS and cloud login systems). Attackers used fake login pages and MFA code theft to steal credentials from employees across multiple industries, including government, education, and healthcare.
Instead of hacking systems directly, attackers relied on users entering credentials and MFA codes into fake portals. This allowed full account takeover and internal system access. Over 150+ organizations were impacted in this identity-focused campaign.
3. MGM Resorts Cyberattack (2023–2024 Impact Spillover)
Although it began in 2023, the impact persisted into 2024 due to weaknesses in identity-based access controls. Attackers used social engineering to trick IT and helpdesk staff into resetting credentials and gaining access to internal systems.
This led to widespread shutdown of hotel operations, digital keys, booking systems, and casino infrastructure. No malware infection was required; only identity manipulation was needed. The attack caused millions in operational losses per day during downtime and highlighted the risks of helpdesk impersonation.
4. AI-Driven SaaS Identity Attacks (2025)
In 2025, attackers increasingly used AI tools to improve identity attacks. They generated realistic phishing emails, fake login portals, and even deepfake voice calls to trick employees into revealing credentials and approving MFA prompts.
This marked a shift where identity attacks became automated, scalable, and harder to detect. SaaS platforms were heavily targeted due to centralized identity systems. Around 75% of organizations experienced SaaS identity-related incidents in 2025.
5. Uber MFA Fatigue Attack (Still Referenced in 2024–2025 Studies)
An attacker repeatedly sent MFA login requests to an employee until they eventually approved one, granting access to internal systems. The attacker used social engineering combined with identity pressure techniques rather than breaking encryption.
Once inside, they accessed internal dashboards, Slack channels, and security tools. MFA fatigue attacks were involved in a significant share of modern identity breaches, with over 50% of incident response cases involving MFA bypass techniques in 2024.
6. Business Email Compromise Surge (2024–2026)
Business Email Compromise (BEC) continued to dominate identity-based cybercrime, where attackers take over corporate email accounts and trick employees into sending money and sensitive data.
In most cases, attackers use stolen credentials and phishing to impersonate executives, making the emails appear legitimate. BEC attacks accounted for 454 of 630 major cyber incidents in recent multi-year analyses, with a sharp increase in 2024–2025.
7. Identity Helpdesk Exploitation (2025–2026 Trend)
A growing attack trend involves targeting IT support teams through voice phishing (vishing). Attackers impersonate employees or executives and convince helpdesks to reset passwords and add new MFA devices.
Once access is granted, attackers move quickly into cloud systems such as Microsoft 365, Slack, and Salesforce without needing malware or system exploitation. Identity helpdesk attacks are now considered one of the fastest-growing entry points in enterprise breaches (2025–2026).
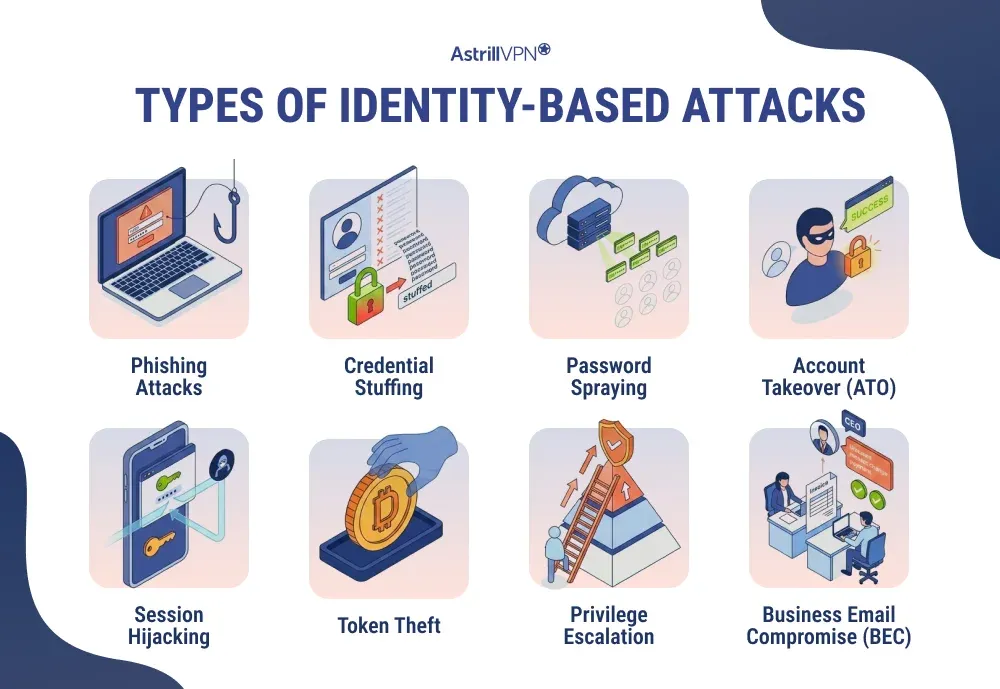
Types of Identity-Based Attacks
There are several common types of identity-based attacks, each using different techniques to compromise user identities.
Phishing Attacks
Phishing is one of the most common types of identity-based attacks, where attackers trick users into revealing their login credentials through fake emails, messages, and websites. These attacks often mimic trusted brands, making them highly convincing. Once users enter their details, attackers can immediately access their accounts.
Credential Stuffing
Credential stuffing involves using stolen username-password combinations from previous data breaches to gain access to multiple accounts. Attackers rely on automated tools to test these credentials across various platforms. Since many users reuse passwords, this method has a high success rate.
Password Spraying
Password spraying is a variant of brute-force attacks in which attackers try a few commonly used passwords across many accounts rather than targeting a single account repeatedly. This helps them avoid account lockouts and detection. It is especially effective in organizations with weak password policies.
Account Takeover (ATO)
Account takeover occurs when attackers gain unauthorized access to a user’s account using stolen credentials. Once inside, they can change account settings, steal data, and perform fraudulent activities. ATO is a direct result of identity compromise and is widespread across banking, social media, and e-commerce platforms.
Session Hijacking
Session hijacking allows attackers to take control of an active user session without needing login credentials. By stealing session cookies or tokens, attackers can access systems as if they were the legitimate user. This type of attack often occurs on unsecured networks and poorly protected web applications.
Token Theft
Token theft involves stealing authentication tokens that are used to verify a user’s identity after login. Once attackers obtain these tokens, they can bypass authentication systems, including multi-factor authentication, and gain direct access to accounts.
Privilege Escalation
Privilege escalation occurs when an attacker gains higher access rights after initially compromising a lower-level account. This allows them to access sensitive systems, data, and administrative controls. It is often used in combination with other identity-based attacks.
Business Email Compromise (BEC)
Business Email Compromise involves attackers gaining access to and impersonating a legitimate business email account. They then send fraudulent emails to employees and partners, requesting payments and sensitive information. As the request appears legitimate, victims are more likely to comply.
Identity-Based Attacks vs Malware Attacks
Identity-based attacks differ significantly from traditional malware attacks in both approach and detection. Malware attacks rely on malicious software such as viruses, ransomware, and trojans to infiltrate systems and cause damage. These attacks often trigger antivirus alerts and require users to download infected files.
In contrast, identity-based attacks do not always involve malicious code. Instead, they exploit valid credentials to gain access, making them much harder to detect with traditional security tools. While malware attacks focus on system vulnerabilities, identity-based attacks target human behavior and authentication systems. As a result, organizations must adopt identity-focused security strategies rather than relying solely on endpoint protection.
How to prevent identity-based attacks?
The following are some proven ways to prevent identity-based attacks.
Implement Strong Authentication Mechanisms
One of the most effective ways to prevent identity-based attacks is by strengthening authentication. Multi-factor authentication (MFA) adds an extra layer beyond passwords, making it harder for attackers to gain access even if credentials are compromised. However, organizations should go further by adopting phishing-resistant methods such as hardware security keys and biometric authentication. Stronger authentication is essential.
Adopt a Zero Trust Security Model
A Zero Trust approach assumes that no user or device should be trusted by default, even if they are inside the network. Every access request must be verified continuously based on identity, device, and behavior. This model limits attackers’ ability to move freely within systems if they gain access.
Use Identity and Access Management (IAM) Solutions
Identity and Access Management (IAM) systems help control who has access to what resources within an organization. By enforcing least-privilege access, users are only given permissions necessary for their roles, reducing the risk of misuse. IAM tools also provide centralized control, making it easier to monitor and manage user identities.
Monitor User Behavior and Detect Anomalies
Continuous monitoring of user activity is essential for detecting suspicious behavior early. Unusual login attempts, such as access from new locations, devices, and abnormal times, can indicate compromised accounts. Behavioral analytics and AI-driven security tools can identify these anomalies in real time.
Strengthen Password Policies and Credential Hygiene
Weak and reused passwords remain a major vulnerability in identity-based attacks. Enforcing strong password policies, encouraging the use of password managers, and regularly updating credentials can help reduce risks. Additionally, organizations should monitor the dark web for leaked credentials and take immediate action if exposure is detected. Since credential misuse is involved in nearly half of all cyber incidents, maintaining proper credential hygiene is crucial.
Educate and Train Users Regularly
Human error is often the weakest link in cybersecurity, especially in phishing and social engineering attacks. Regular training helps users recognize suspicious emails, fake login pages, and unusual authentication requests. Awareness programs can significantly reduce the chances of credential theft.
Deploy Advanced Security Tools (ITDR & EDR)
Advanced tools such as Identity Threat Detection and Response (ITDR) and Endpoint Detection and Response (EDR) provide deeper visibility into identity-related activities. These tools help detect compromised accounts, unusual privilege escalations, and lateral movement within networks. By combining identity-focused and endpoint security, organizations can create a more comprehensive defense.
Secure Sessions and Tokens
Attackers often target session tokens to bypass authentication without having to re-enter credentials. Securing sessions through token expiration policies, encrypted communications, and re-authentication for sensitive actions can reduce this risk. Organizations should also monitor for token misuse and revoke access when suspicious activity is detected. As token-based attacks grow more sophisticated, securing sessions becomes a critical part of identity protection.
Conclusion
Identity-based attacks have become the leading cause of modern data breaches, overtaking traditional malware-driven threats. By exploiting user credentials and authentication systems, attackers can bypass security defenses and operate undetected. With over 80% of breaches now linked to compromised identities, organizations must prioritize identity security through strong authentication, continuous monitoring, and user education. In 2026 and beyond, protecting digital identities is no longer optional; it is a core pillar of cybersecurity.
FAQs
Here are some of the frequently asked questions.
Attackers bypass MFA using tactics like MFA fatigue, real-time phishing, and session hijacking. Phishing kits can capture both passwords and OTPs instantly, while SIM swapping intercepts SMS codes.
Account takeover (ATO) happens when attackers gain control of a user account using stolen credentials. It is a direct form of identity-based attack because it relies on impersonating legitimate users rather than exploiting software flaws.
Once attackers log in, they use the same identity to access other systems, shared files, and admin tools. As the access appears legitimate, they can quietly move deeper into the network.
Early signs include unusual login locations, impossible travel activity, repeated login failures, and sudden privilege changes. Behavioral analytics tools can flag these anomalies in real time.
Key tools include IAM (Identity & Access Management), MFA, Zero Trust frameworks, and ITDR solutions. These ensure strict access control and continuous user verification.


No comments were posted yet