What Is a VPN Concentrator and How Does It Work?

Arsalan Rathore

Most people know what a VPN is. You install an app, hit connect, and your traffic routes through an encrypted tunnel. Simple, effective, and built for one device at a time.
Now imagine you’re an IT administrator responsible for keeping 2,000 remote employees securely connected to a corporate network, from different cities, different devices, and different time zones, all at the same time. A standard VPN setup would buckle under that kind of pressure.
That’s exactly the problem a VPN concentrator solves. It’s enterprise infrastructure, not a consumer product. And if you’re evaluating remote access options for your organization, understanding how it works is worth your time.
Table of Contents
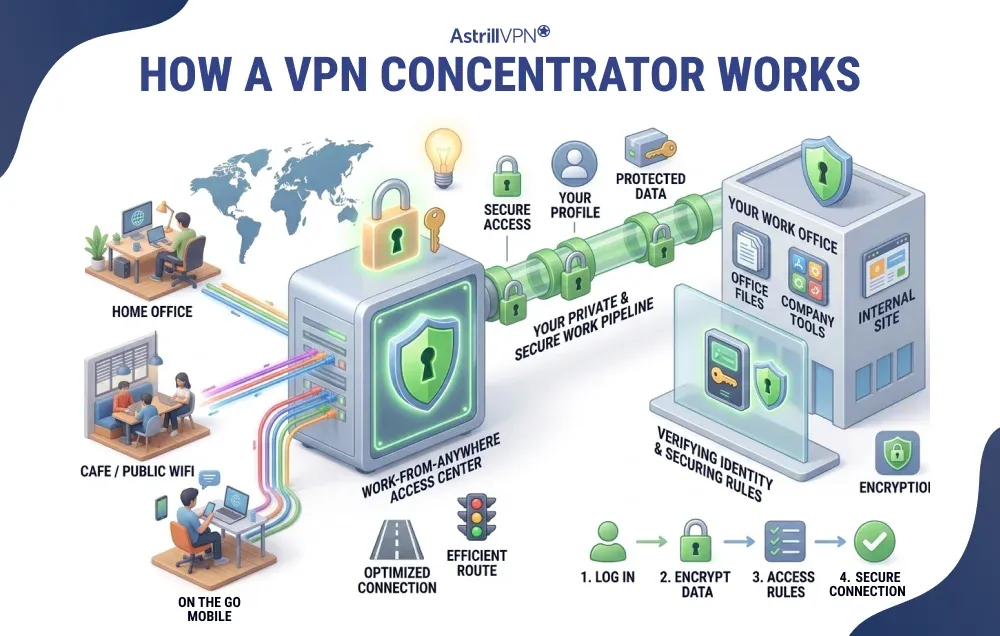
How does a VPN Concentrator work?
At its core, a VPN concentrator is a dedicated network device that manages a large number of simultaneous VPN connections from a single, centralized point. Think of it as the hub that all remote workers connect through before they can access anything on the corporate network.
Here’s what happens when a remote employee connects:
- The VPN client on their device initiates a connection to the concentrator.
- The concentrator verifies their identity through an authentication process, checking credentials before granting access.
- Once authenticated, the concentrator assigns the user a unique IP address within the network.
- It opens an encrypted tunnel between the user’s device and the corporate network.
- All traffic moving through that tunnel is encrypted on the way out and decrypted on arrival, keeping it unreadable to anyone intercepting it in transit.
Key Features and Capabilities
A VPN concentrator does more than just open encrypted tunnels. Here’s what you actually get with enterprise-grade deployment:
- Simultaneous tunnel management: The concentrator can maintain thousands of encrypted VPN tunnels at the same time, each independent and secure.
- User authentication: It verifies every user before granting network access, typically integrating with directory services like Active Directory or LDAP.
- IP address assignment: Each authenticated user gets a unique IP, which administrators can use for whitelisting, access controls, and monitoring.
- Traffic load balancing: Incoming connections are distributed efficiently so no single point gets overwhelmed, keeping performance stable even during peak usage.
- Network segmentation: Admins can assign different access privileges to different users or groups, limiting how far into the network someone can reach based on their role.
- Identity obfuscation: Encrypted tunnels hide metadata like IP addresses and port numbers, reducing the visibility of user activity on the public internet.
- SaaS application access: Modern concentrators can establish private tunnels directly to cloud-based applications, not just internal servers.
- Centralized monitoring: All connection activity flows through one point, making it easier to detect anomalies, log activity, and respond to incidents quickly.
VPN Concentrator Use Cases in Business
VPN concentrators show up wherever scale, control, and security overlap. Here are the environments where they genuinely earn their place.
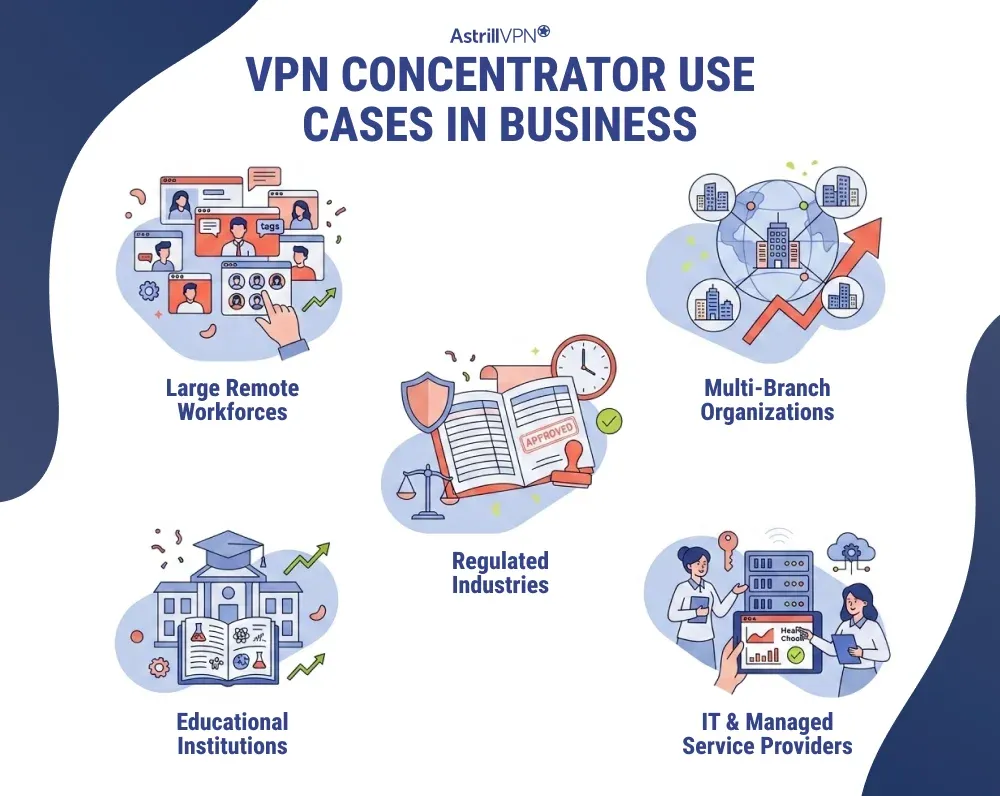
Large Remote Workforces
This is the most straightforward use case. Any organization with hundreds or thousands of employees working remotely needs a solution that won’t degrade under load. A concentrator ensures every employee gets a stable, encrypted connection to internal systems, whether they’re logging in from home, a hotel, or a branch office.
Multi-Branch Organizations
Companies with multiple office locations often need those offices to communicate securely without routing traffic through the public internet. A VPN concentrator can serve as the central hub in a hub-and-spoke model, connecting regional branches to headquarters through dedicated encrypted tunnels.
Regulated Industries
Healthcare organizations dealing with patient records, financial institutions managing sensitive transaction data, and government agencies handling classified information all operate under strict compliance requirements. VPN concentrators give these organizations the centralized access control and audit trail they need to satisfy regulatory standards like HIPAA, PCI-DSS, and others.
Educational Institutions
Universities and large school districts often need to give thousands of students, faculty, and staff access to internal systems and licensed resources. A concentrator handles that scale without forcing administrators to configure individual client connections one by one.
IT and Managed Service Providers
MSPs managing networks for multiple client organizations use concentrators to maintain secure, segmented access to each client environment. The segmentation capability ensures that access to one client’s network never bleeds into another’s.
Benefits of Using a VPN Concentrator
When the scale and security requirements are right, a VPN concentrator delivers advantages that simpler solutions can’t match.
- Centralized management: Instead of managing VPN configurations across dozens of routers or individual client setups, administrators can control everything from a single location. Policy changes, user revocations, and access updates happen centrally and propagate immediately.
- Scalability: As an organization grows, the concentrator grows with it. Most enterprise-grade units can handle capacity increases without requiring a full infrastructure overhaul.
- Consistent security enforcement: Every connection passes through the same authentication and encryption standards. There’s no risk of someone using a misconfigured router or outdated protocol to access the network.
- High availability: Enterprise concentrators are typically deployed with redundancy built in, so a hardware failure doesn’t take down remote access for the entire organization.
- Improved performance at scale: Load balancing across tunnels prevents any single connection from degrading the experience for everyone else.
Limitations and Drawbacks
A VPN concentrator is not the right tool for every situation. Before investing, it’s worth being honest about the downsides.
High upfront cost
Enterprise-grade hardware doesn’t come cheap. Depending on the number of tunnels and throughput requirements, the initial investment can run from several hundred to tens of thousands of dollars, not counting the infrastructure to support it.
Specialized expertise required
Configuring and managing a VPN concentrator isn’t something a generalist IT staffer can typically do without training. Many organizations end up contracting specialized engineers, which adds to the total cost.
Bandwidth limitations
Every concentrator has a ceiling on how much traffic it can process. If your user base scales faster than your infrastructure, you’ll hit performance bottlenecks before you can add capacity.
Single point of failure risk
Centralization is its biggest strength and its most significant vulnerability. If the concentrator goes down and there’s no redundant system in place, everyone loses remote access simultaneously.
Overkill for small teams
For organizations with fewer than a few dozen remote users, the complexity and cost of a concentrator rarely makes sense. Simpler solutions handle that load without the overhead.
VPN Concentrator vs. VPN Router
This is probably the most common comparison people make when evaluating remote access options.
A VPN router is a standard network router with VPN functionality built in. It works well for small offices or home setups where you need a handful of secure connections. It’s cheaper, simpler to set up, and doesn’t require specialized knowledge to maintain.
A VPN concentrator is a VPN router that’s been purpose-built for scale. It handles far more simultaneous connections, supports more complex protocols, and gives administrators granular control over access policies. The tradeoff is cost and complexity.
If you’re running a 10-person team, a VPN router is almost certainly enough. If you’re managing remote access for 500 employees across three continents, a concentrator is the right choice for your infrastructure.
VPN Concentrator vs. VPN Gateway
These two terms get used interchangeably, but they’re not quite the same thing.
A VPN gateway is a broader term for any central node in a VPN architecture that manages connections between networks. That category includes VPN concentrators, cloud-based VPN gateways, and software-defined solutions.
A VPN concentrator is a specific type of VPN gateway, typically referring to a dedicated hardware appliance designed to handle high-volume tunnel management. It’s a subset of the gateway category, not a synonym for it.
When vendors market a product as a “VPN gateway,” they may be referring to a cloud-based solution or a software-defined appliance. When they say “VPN concentrator,” they’re usually talking about a physical or virtual device optimized specifically for managing large numbers of tunnels.
VPN Concentrator vs. Site-to-Site VPN
These serve different connectivity needs, and understanding the difference matters for network design.
A site-to-site VPN creates a permanent, encrypted connection between two fixed locations. A company’s headquarters in New York and its office in London might be linked via a site-to-site VPN, allowing both locations to share internal resources as if they were on the same local network.
A VPN concentrator handles point-to-site connections, connecting individual remote users to the corporate network. Each user gets their own encrypted tunnel, authenticated separately, and subject to individual access policies.
The two aren’t mutually exclusive. Many enterprise networks use site-to-site VPNs to connect office locations, while a VPN concentrator handles remote access for individual employees. Both can run through the same infrastructure.
Protocols Supported by VPN Concentrators
VPN concentrators don’t just create tunnels. They manage the protocols that determine how data moves through those tunnels and how it gets encrypted. Most enterprise concentrators support several protocols simultaneously, allowing administrators to choose the right one for each use case.
- IPsec: The most widely used protocol for enterprise VPNs. It operates at the network layer, encrypting entire IP packets, and is particularly well-suited for site-to-site tunnels and stable remote access. Most modern hardware supports it natively.
- SSL/TLS: Browser-based protocols that allow users to connect through a web browser without installing a separate VPN client. Useful for organizations where client software deployment is impractical or restricted.
- L2TP/IPsec: Layer 2 Tunneling Protocol combined with IPsec for encryption. A legacy choice that’s still useful for connecting older devices that don’t support newer protocols.
- PPTP/MPPE: An older tunneling protocol with known security vulnerabilities. Most enterprise environments have moved away from it, though some legacy systems still rely on it. Generally considered obsolete for new deployments.
- DMVPN: Dynamic Multipoint VPN, pioneered by Cisco, simplifies the configuration of large-scale site-to-site IPsec networks. It allows concentrators to build tunnels dynamically between remote sites without pre-configuring every connection individually.
VPN Concentrator Deployment Options
VPN concentrators aren’t one-size-fits-all hardware boxes anymore. Organizations have several deployment paths depending on their infrastructure, budget, and technical capacity.
Dedicated hardware appliances
The traditional approach. A physical device, sized for the expected number of connections, is installed at the network edge. Hardware appliances offer predictable performance and are purpose-built for the task. Cisco Meraki and Aruba are common choices here.
Virtual appliances
Software versions of the concentrator that run inside a VM or container environment. Cloud deployments increasingly rely on this model, allowing organizations to scale resources up or down without buying new hardware.
Cloud-hosted concentrators
Fully cloud-based solutions managed by the vendor. These reduce on-premises hardware requirements and work well for organizations that have already moved most of their infrastructure to the cloud.
Open source solutions
For organizations with technical staff and tighter budgets, open-source projects such as OpenVPN, pfSense, VyOS, and native Linux implementations can be configured as VPN concentrators. The tradeoff is that setup and maintenance require meaningful IT expertise.
Popular VPN Concentrator Brands
The enterprise VPN concentrator market is dominated by a handful of well-established vendors. Here’s a brief look at the most common ones:
Cisco Meraki
One of the most widely deployed options in enterprise environments. Cisco’s concentrators are known for being relatively straightforward to set up and manage, even for large organizations. They’re built to scale and integrate well with the broader Cisco ecosystem.
Aruba (HPE)
Hewlett Packard’s Aruba product line includes VPN concentrator solutions that integrate well with both wireless and wired network infrastructure. A strong choice for organizations already invested in the HPE stack.
ShoreTel (now Mitel)
Focused primarily on remote IP telephony. Their VPN concentrators are designed to extend a company’s phone system securely to remote workers, rather than general-purpose network access.
Palo Alto Networks
More commonly associated with next-generation firewalls, but their GlobalProtect platform functions as a VPN concentrator with strong integration into their broader security infrastructure.
Open source options
OpenVPN, pfSense, and VyOS give technically capable teams flexible, cost-effective alternatives to commercial hardware. OpenVPN is particularly popular for smaller deployments and organizations that need a highly customizable setup.
What If You Don’t Need a Concentrator?
VPN concentrators are built for scale, and that’s precisely what makes them the wrong fit for most people. If you’re an individual, a freelancer, or part of a smaller team, you don’t need a rack-mounted appliance and a dedicated network engineer to stay secure online. You need something that works, works fast, and doesn’t require an IT department to manage it.
That’s where AstrillVPN comes in. It gives you the same foundational benefits a concentrator is built around, which are strong encryption, secure tunneling, and consistent privacy protection, without any of the infrastructure overhead. You get support for industry-standard protocols including WireGuard, OpenVPN, and StealthVPN, a strict no-logs policy, and connection speeds that don’t make you feel like you’re paying a privacy tax every time you browse.
For individuals and small businesses, AstrillVPN is the practical answer to the same question a concentrator tries to solve at enterprise scale: how do you stay private, secure, and in control of your connection? With Astrill, you get that without the hardware, the complexity, or the five-figure price tag.
Who Should (and Shouldn’t) Use a VPN Concentrator
The honest answer is that most organizations don’t need a VPN concentrator, and that’s completely fine. A VPN concentrator makes sense if your organization has hundreds or thousands of remote users who need reliable, secure access to corporate resources. It also makes sense if you operate in a regulated industry where centralized access control and audit logging are not optional. Multi-branch organizations that need to interconnect office locations at scale also benefit significantly.
If you’re a small business, a startup with a distributed team of 50 people, or an organization where most employees work on-site, a VPN concentrator introduces complexity and cost that far outpace the benefits. A good VPN router, a cloud-based remote access solution, or even a properly configured software VPN will serve you better for a fraction of the investment.
The deciding factor comes down to scale and control requirements. If you need to manage thousands of connections with granular access policies, centralized monitoring, and consistent encryption standards across the board, a concentrator is the right call. If you don’t, it isn’t.
FAQs
A VPN concentrator is used to create, manage, and secure multiple VPN connections simultaneously. It helps organizations efficiently handle large volumes of encrypted remote access traffic, especially for employees working remotely.
A VPN server provides VPN access for individual users or smaller groups, while a VPN concentrator is built to support many simultaneous VPN tunnels in enterprise environments. A concentrator offers better scalability, stronger traffic management, and centralized security controls.
Businesses use VPN concentrators to provide secure remote access for employees, branch offices, and partners. They help improve performance, reduce network strain, centralize VPN management, and enforce stronger authentication and encryption policies.
VPN concentrators commonly support protocols such as IPsec, SSL VPN, L2TP, PPTP, and, in some cases, GRE, depending on the device and vendor. IPsec and SSL VPN are the most commonly used due to their stronger security.
A VPN gateway connects entire networks securely, usually for site-to-site VPN communication between offices. A VPN concentrator is primarily designed to manage and scale multiple remote-user VPN connections. A gateway focuses on network-to-network connections, while a concentrator focuses on user-to-network access.


No comments were posted yet