What is Wave Browser, And How Can You Uninstall it?

Bisma Farrukh
Wave Browser appears to be a regular browser on the surface, but it’s a type of software you might not want on your computer. This misleading browser can collect your data without your knowledge, bombard you with intrusive advertisements, and be quite challenging to uninstall.
In this guide, we’ve discussed everything related to the Wave browser in detail so that you can learn more about this malicious software and how to uninstall it if you’ve got it in your system.
Table of Contents
What is Wave browser?
Wave Browser was developed in 2015 as a web browser, but it’s a potentially unwanted program. Its continued use has resulted in numerous user issues and vulnerabilities.
Polarity Technologies LTD, the company behind the development of Wave Browser, has distributed it across various countries. It functions as a subsidiary of the Chinese firm Genimous Technology Co Ltd, which has faced accusations of building a search hijacking empire.
The Wave browser is a web browser that looks a lot like Chrome, but it comes with some warnings from experts. This browser is based on Chromium, the same platform Chrome uses, but there are concerns about data security and privacy.
The problem lies in the intrusive and annoying ads and links that the Wave browser displays. Some of these ads and links may hide viruses or malware.
If you click on one of these harmful ads or links, a browser hijacker could take over your browser. This means that someone else could control your device. Moreover, these ads or links might install spyware on your computer, which can secretly collect and track your personal information.
Everything you do in your browser, such as making online payments or accessing your bank accounts, becomes accessible to cybercriminals. They could even sell your valuable information on the black market. Be cautious when using the Wave browser due to these potential security and privacy risks.
How Does Wave Browser Get Installed on Your Device?
Like other software, the Wave browser finds its way onto your computer when you install it intentionally or unintentionally. It’s a downloadable application, just like Chrome or Firefox, which you can get from the internet and set up on your computer.
Sometimes, this browser can sneak into your computer bundled with other programs you install. You might not even notice it as an optional addition, especially if you rush through the installation process or overlook customization options. These additional programs often go by names like “bloatware” or “unwanted programs.”
Here’s the catch: some programs, like the Wave browser, can be browser hijackers or even carry malicious software. Suddenly, your device might show signs of a wave browser malware infection.
Sometimes, you’ll spot these unwanted programs in your operating system’s menus or hard drive. But others hide deep within less obvious folders or your system’s registry, making them harder to spot. Be vigilant during installations to avoid these surprises.
Is Wave Browser Safe?
The Wave browser is unsafe because it can harm your device, particularly when displaying harmful ads or directing you to fake websites designed to steal your personal information. It’s important to understand that it’s not a virus or malware but a potentially unwanted program.
Is Wave Browser a Virus?
Unlike viruses, it doesn’t spread or directly infect your device. Instead, it typically ends up on your device by accident, often through tricky methods, not malicious scripts, to gather your information. To stay safe, it’s advisable to remove it from your device.
14 Indications of the Wave Browser Virus
The following are indicators of the presence of the Wave browser on your computer:
1. Increased Pop-Up Ads
You start noticing a sudden increase in pop-up advertisements while browsing. These pop-ups often appear on websites where you wouldn’t typically expect them, disrupting your online experience.
2. Homepage Changes
The homepage of your web browser is altered without your consent. It may redirect to unfamiliar websites or search engines, often designed to generate ad revenue or promote specific products or services.
3. Search Engine Modifications
Your default search engine settings are modified to a different, unfamiliar one. Your search results may also be tampered with, showing additional sponsored links or unrelated content.
4. Slower Browsing
Your web browser’s performance becomes noticeably slower. Pages take longer to load, and the browser may freeze or crash more frequently. These issues can result from the resource-intensive nature of unwanted extensions or background processes.
5. Unwanted Browser Extensions
New browser extensions, toolbars, or add-ons appear in your browser seemingly out of nowhere. While some claim to offer valuable features, they may primarily serve as adware, displaying more ads and tracking your online activity.
6. Browser Homepage Locking
Attempts to change your browser’s homepage or search engine settings are resisted. The PUP may automatically revert these changes, making it challenging for you to regain control over your browser preferences.
7. Suspicious Toolbars
You notice unfamiliar toolbars at the top of your browser window, often containing shortcuts to websites or services you didn’t intend to use. These toolbars can clutter your browser interface.
8. Browser Crashes
Frequent browser crashes or instability become commonplace. Your browser may unexpectedly close or become unresponsive, making it difficult to use for everyday tasks.
9. Unfamiliar Programs
A closer look at your installed programs reveals unfamiliar software you should have knowingly downloaded or installed. These programs may have arrived bundled with other software.
10. Unauthorized Data Collection
Concerns arise about the extent of data collection by the PUP. Without explicit consent, it may track your browsing habits, search history, and even personal information.
11. Increased Network Activity
Unwanted programs can generate heightened network activity, increasing data usage even when you’re not actively using your browser. This can impact your internet performance and data usage limits.
12. Security Warnings
Your computer’s security software may issue warnings or alerts regarding potentially harmful activities associated with the Wave browser or similar PUPs. These warnings should not be ignored.
13. Difficulty in Removal
The unwanted program may resist straightforward uninstallation. It might leave behind remnants or reinstall itself, necessitating more comprehensive removal methods or the use of specialized software.
14. Suspicious File Downloads
You come across files or software downloads that you still need to initiate. These downloads may be linked to the activities of the unwanted program and could pose security risks.
How to remove Wave browser?
Following are some of the ways to remove the Wave Browser from your device:
How to uninstall Wave browser on Windows
- Press the Windows key, type “Settings” and press Enter.
- In the Settings menu, select “Apps”.
- Now, you’ll see a list of all installed apps. Locate “Wave Browser” in the list.
- Click on “Wave Browser” and then click the “Uninstall.”
- Now open Task Manager by typing it in the start menu search bar.
- In the list of “processes,” look for processes related to the Wave browser.
- Once located, right-click on it and select “Open file location”.
- Delete everything in that folder by selecting all files and pressing “shift+delete.”
- Now go back to the task manager, click on the Wave browser process, and select “End Task.”
- Now press “Windows key +R” to open the “Run” dialog box.
- Once the Run window opens, type “regedit” and click “OK.”
- Press “ctrl+F,” type “Wave,” and click “Find Next.”
- Delete all files related to the Wave browser in the system registry.
- Once done, restart your computer.
How to uninstall Wave browser on a Mac
- Open the Finder by clicking on the Finder icon in the Dock.
- In the Finder window, go to the “Applications” folder.
- Find the “Wave Browser.”
- In the context menu that appears, select “Move to Bin” to send the Wave Browser to the Trash.
- Right-click the Trash icon in the macOS taskbar and choose “Empty Bin.”
How to uninstall Wave browser on Android
- Open the “Settings” app on your Android device.
- Scroll down and find the “Apps” option.
- Locate “Wave Browser” in the list of installed apps.
- Tap on “Wave Browser” and then tap the “Uninstall” button.
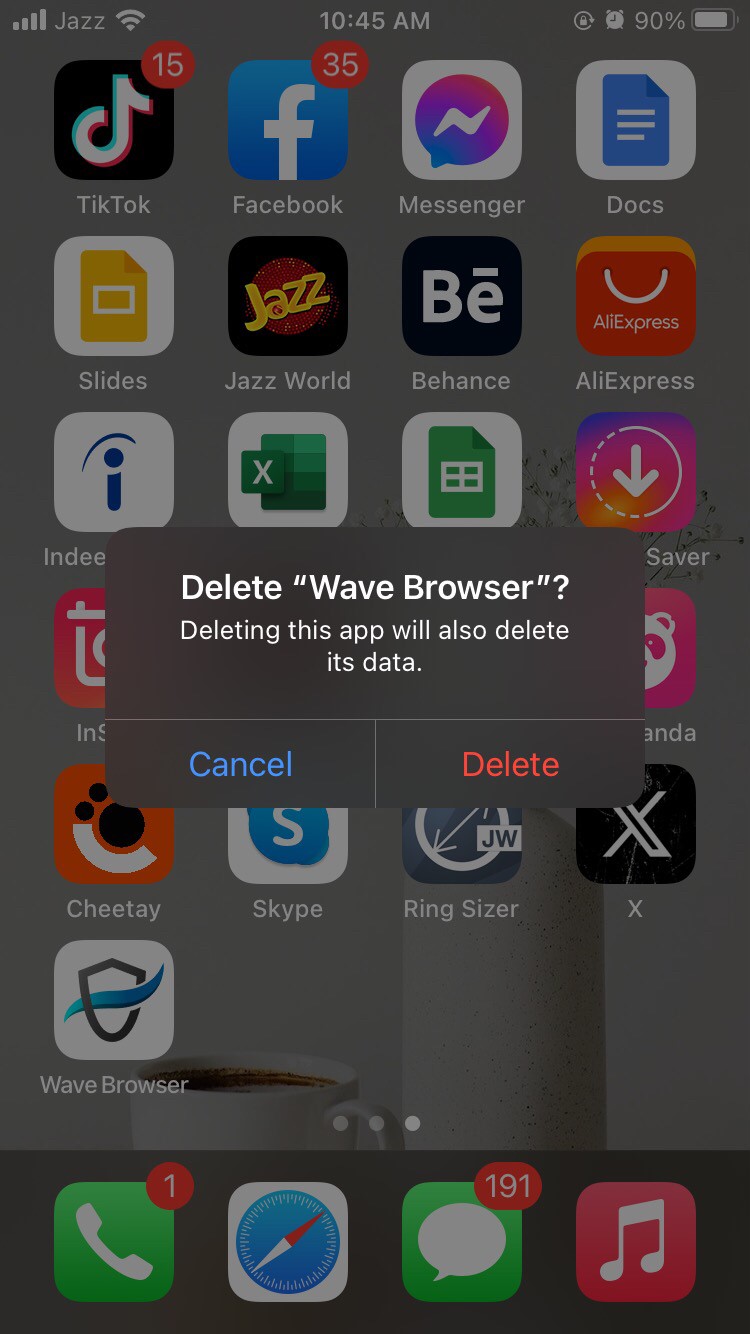
How to uninstall Wave browser on iOS
- On your iOS device’s home screen, find the Wave Browser icon.
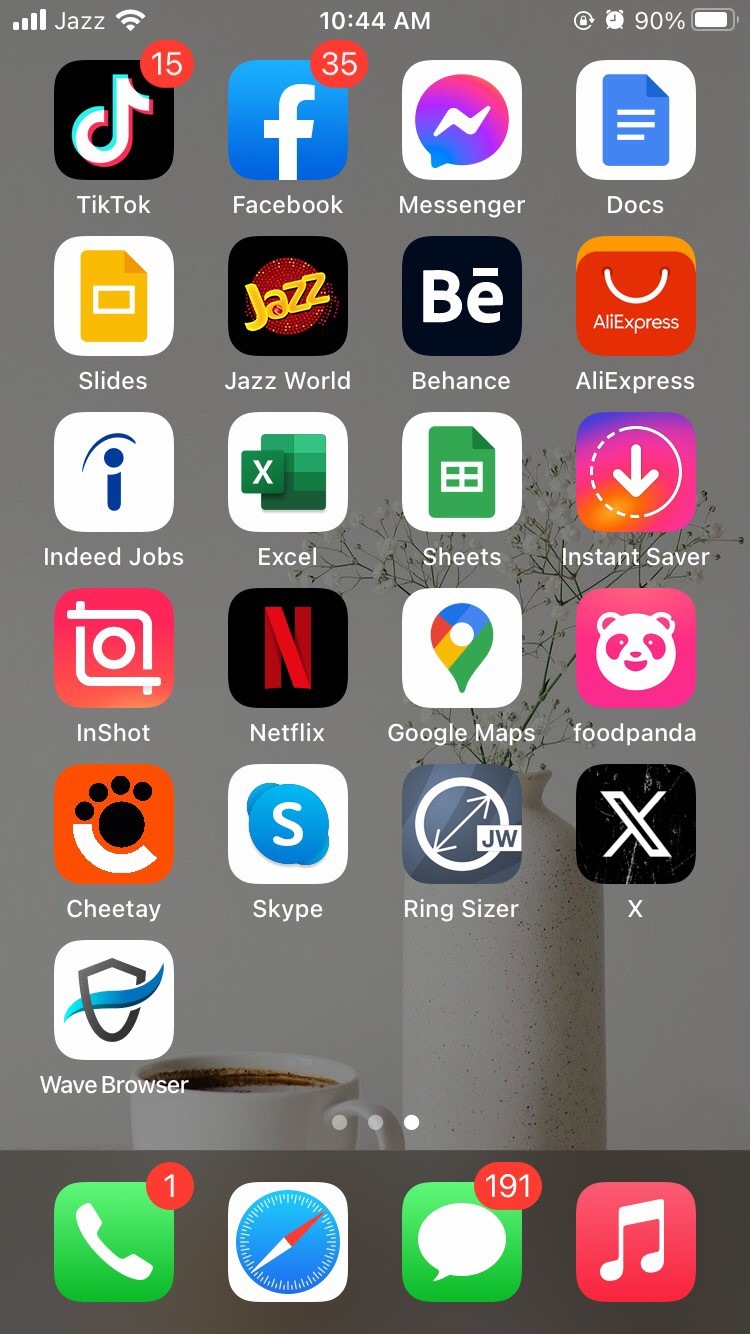
- Long-press on the app icon until it jiggles and an “X” appears in the top-left corner of the icon
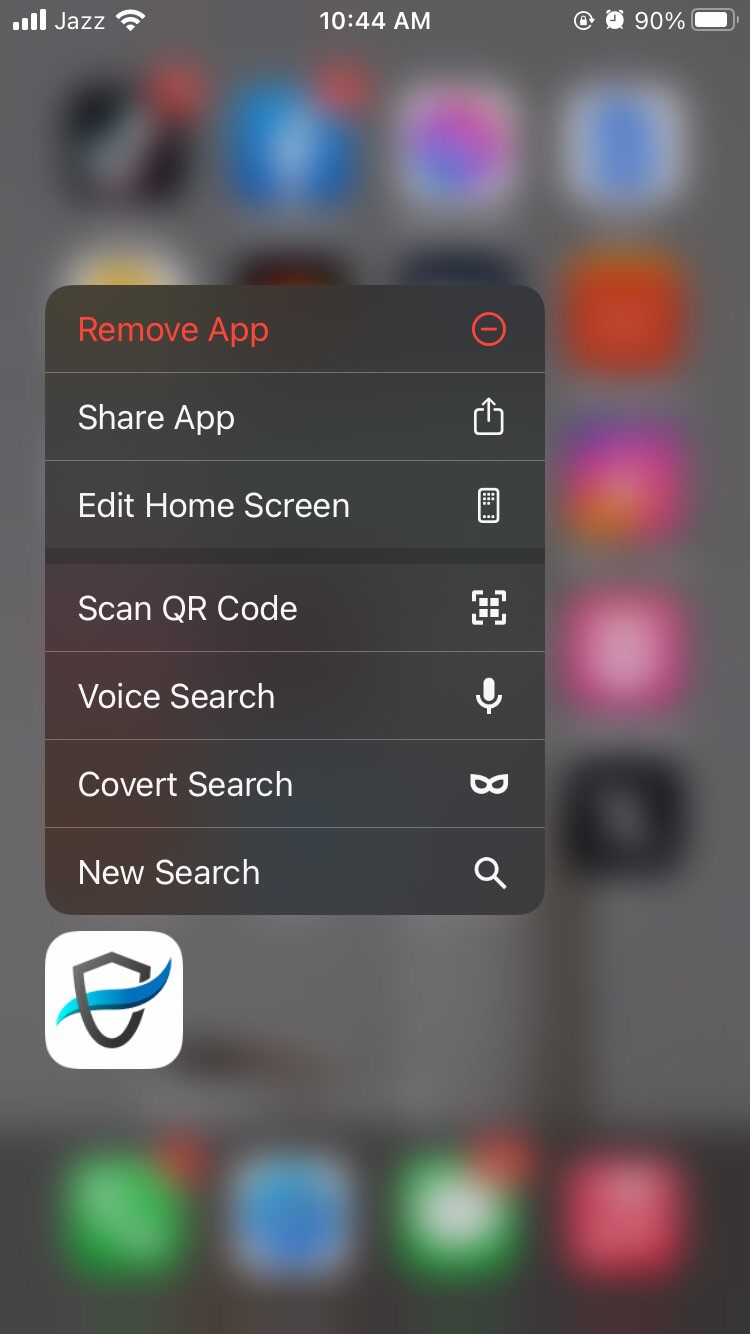
- Tap the “X” on the Wave Browser icon, then confirm the deletion when prompted.
How to fix your browser’s settings after Wave browser removal
How to reset browser settings in Chrome
- Launch the Google Chrome browser.
- Click on the three vertical dots in the top-right corner of the browser window to open the menu.
- From the menu, hover over “Settings” and click on it to access the settings page.
- Scroll down to the bottom of the settings page and click on “Advanced” to reveal more options.
- Under the “Reset and clean up” section, click “Restore settings to their original defaults.”
- A confirmation dialog will appear. Click on “Reset settings” to confirm.
- After resetting, Chrome will restart to apply the changes. Your browser settings will be restored to their default state.
How to reset browser settings in Firefox
- Launch the Mozilla Firefox browser.
- Click on the three horizontal lines (menu icon) in the top-right corner of the browser window to open the menu.
- Click ” Options ” from the menu to access the settings page.
- In the left-hand menu, scroll down and click on “Help.” Then, click on “Troubleshooting Information.”
- Find the “Refresh Firefox” button on the Troubleshooting Information page on the right-hand side.
- Click “Refresh Firefox” and confirm your choice in the dialog box.
- After resetting, Firefox will close and reopen automatically to apply the changes. Your browser settings will be reset to their default state.
How to Prevent the Wave Browser from Getting in your Device

To prevent the Wave browser and other potentially unwanted programs (PUPs) from infiltrating your devices, follow these proactive measures:
1. Download Software from Trusted Sources
Always download software and applications from reputable sources, such as the official websites of the software developers or trusted app stores like Google Play or Apple App Store. Avoid third-party download sites and torrents, which often host malicious software versions.
2. Read Installation Prompts Carefully
During the installation process, pay close attention to the prompts and options. Opt for custom or advanced installation settings whenever available. This allows you to review and deselect any additional software or toolbars bundled with the main program.
3. Keep Your Operating System and Software Updated
Regularly update your operating system, web browsers, and all installed software. Developers release updates and security patches to fix vulnerabilities and weaknesses that PUPs and other malicious software can exploit.
4. Use Security Software
Utilizing robust security software is one of the most critical steps in safeguarding your computer against potentially unwanted programs (PUPs) and online threats. Antivirus and anti-malware software shield against potentially unwanted programs (PUPs) and other online threats. They continually scan your system for malicious activity, offer real-time protection, and receive regular updates to stay current with emerging threats.
In conjunction with security software, consider using a VPN because it enhances your online security by encrypting your internet connection, making it difficult for cybercriminals to intercept your data.
Opt for a reliable VPN like AstrillVPN because It provides anonymity by masking your IP address, granting access to restricted content, and safeguarding your privacy on public Wi-Fi networks. Security software and AstrillVPN offer comprehensive protection against PUPs and bolster your online privacy and security.
5. Enable Firewall Protection
Enable your computer’s built-in firewall, or consider using a third-party firewall application. Firewalls act as a barrier between your computer and potentially harmful content on the internet.
6. Be Cautious with Email Attachments and Links
Exercise caution when dealing with email attachments and links, especially emails from unknown or suspicious senders. Some PUPs can be distributed via email attachments or phishing links.
7. Regularly Backup Your Data
Create and maintain regular backups of your essential data on an external drive or cloud storage. In case your computer becomes compromised, you can restore your data without paying ransomware fees.
8. Use a Standard User Account
Avoid using an administrator account for everyday tasks. Instead, use a standard user account for routine activities. This limits the permissions of potentially harmful software and reduces the damage they can cause.
9. Use Browser Security Extensions
Consider installing browser security extensions or add-ons that can help block malicious websites, intrusive ads, and harmful scripts. These extensions can add an extra layer of protection to your online activities.
10. Regularly Review Installed Programs
Periodically review the list of installed programs on your computer. Uninstall any software that you no longer need or trust. This reduces the potential attack surface for PUPs.
11. Set Browser Security and Privacy Preferences
Adjust your web browser’s settings to enhance security and privacy. Configure pop-up blockers, enable safe browsing features, and set preferences to limit cookies and tracking. Exercise caution when encountering offers or downloads that seem too good to be true. Avoid downloading software or clicking links that promise unrealistic benefits or prizes, as they may lead to PUP installations.
FAQs
Yes, removing the Wave browser is recommended, especially if you didn’t intentionally install it. It is considered a potentially unwanted program (PUP) and may pose security and privacy risks.
No, the Wave browser is not part of Microsoft. It is a separate web browser application that resembles popular browsers like Chrome or Firefox.
The Wave browser is not a hack but can be considered potentially unwanted software. Some users may install it unknowingly, and it can exhibit intrusive behavior, such as displaying invasive ads or changing browser settings.
In Google Chrome, “Wave” is not a standard term or feature. If you refer to a specific extension or application, it may not be a well-known or official browser component.
The Brave browser is considered safe and privacy-focused. It includes features like ad-blocking and enhanced privacy settings.
The Wave browser is not typically classified as a Trojan. It is primarily categorized as a potentially unwanted program (PUP).


No comments were posted yet