Blogs Posted by Bisma
All of us know that the internet would not function without bots. From search engines indexing billions of web pages to chatbots providing instant customer support, bots automate tasks, improve efficiency, and enhance user experiences. However, not all bots serve beneficial purposes; malicious bots silently infiltrate systems, steal sensitive data, manipulate traffic, and even crash […]
In our hyperconnected world, billions of devices access the Internet every second. The Domain Name System (DNS) is a silent yet crucial component often called the “phonebook of the Internet.” It translates human-readable domain names into machine-readable IP addresses. While this process seems simple on the surface, DNS is a high-value target for cybercriminals. This […]
Distributed denial-of-service (DDoS) attacks remain one of the most common and disruptive cyber threats today. In 2024, industry telemetry shows that large-scale DDoS events continue to occur frequently and that peak attack volumes in recent years have reached hundreds of gigabits per second. Among DDoS techniques, the SYN flood (sometimes called SYN flooding) is a […]
You’re traveling abroad and suddenly realize you can’t access TextNow, your favorite messaging app. Whether you’re trying to unblock TextNow from a restricted country or dealing with TextNow not working issues due to geographic limitations, this comprehensive guide will show you exactly how to regain access from anywhere in the world. What Is TextNow and Why You Might Want […]
If you’re on the lookout for a perfect mobile app that allows you to call and message people over the internet for free, then Talkatone is the app that needs to pique your interest. Talkatone used voice-over-internet protocol (VoIP technology), allowing you to to communicate with your friends and loved ones without incurring high roaming […]
Have you ever wondered why the Wi-Fi on your phone automatically connects when you get home? It’s because network devices like routers use MAC addresses( unique identifiers hardwired onto network interface cards) to recognize trusted devices. But MAC addresses aren’t always permanent. According to latest report, as of 2025, almost all modern smartphones including every […]
A VPN authentication error occurs when the server cannot verify your login credentials or the connection parameters. This can happen for a variety of reasons, including incorrect usernames or passwords, outdated VPN clients, protocol mismatches, or network restrictions. Understanding why these errors occur is the first step toward resolving them quickly and effectively. In this […]
If you’re just minding your own business when an email pops into your inbox from Facebook and the subject line says your Facebook account’s recovery code is inside. Scammers are getting craftier with phony account recovery emails. If this sounds familiar, you’re not alone. Lots of folks are getting duped by fake Facebook account recovery […]
Have you noticed your internet speed slowing down recently, especially when streaming your favorite shows or gaming online? You start to wonder if your internet service provider, Spectrum, could be throttling your connection. Spectrum claims they don’t throttle internet speeds, but many customers report slower speeds during peak usage times. We’ve got some tips to […]
Organizations rely heavily on web applications, cloud services, and complex IT infrastructure. But amidst the growing sophistication of technology lies a silent yet devastating vulnerability: security misconfiguration. Often overlooked, this vulnerability allows attackers to exploit weak spots in systems that were improperly set up, inadequately maintained, or simply neglected. According to IBM’s 2025 Cost of […]
In today’s hyper-connected digital landscape, your devices face constant threats from malicious software. In fact, experts estimate there will be nearly 6.5 billion malware infections worldwide in 2025, with 300,000 new malware samples created every day. These digital threats can compromise your data, financial information, and overall cybersecurity, from viruses and worms to trojans and […]
In 2025, the idea that once something goes on the internet, it’s there forever is no longer just a fear. From public records and data breaches to social media profiles and third‑party brokers, our personal information is scattered in hundreds of places. But it doesn’t have to be that way. In this article, we’ll explore […]
Cyber threats are evolving faster than ever, and they’re targeting endpoints. In fact, according to a 2024 report by IDC, 70% of successful cyberattacks now begin at the endpoint. While still useful, traditional antivirus software is no longer enough to stop modern, sophisticated threats like ransomware, zero-day exploits, and fileless malware. As organizations adopt remote […]
You’ve probably heard of mobile hotspots by now. They’re an amazing way to get online anywhere and can be life-saving when traveling. But what happens if someone gets their hands on your hotspot password? Now, you have to assess whether mobile hotspots are secure. They could potentially harm your privacy. Fortunately, there are several methods […]
In this fast-paced world, mobile work is increasing, and the need for secure remote access is a constant issue faced by workers. That’s why remote access VPNs are becoming increasingly popular. Suppose you’re out of town on a business trip and realize you left your laptop charger at home. You need access to some files […]
Cybercriminals increasingly employ spoofing to deceive targets and gain unauthorized access to systems. In 2025, researchers identified 3.7 billion URL-based threats in just six months. Attackers increasingly relied on AI-generated content, QR codes, and SMS for credential phishing. Phishing makes up 40% of spear-phishing attacks. Over 1 billion phishing emails are sent daily. These attacks exploit […]
In the fast-paced world, individuals manage numerous passwords for different platforms and services. This often leads to security lapses, weak credentials, and user frustration. Single Sign-On (SSO) addresses these challenges by streamlining access and enhancing security. SSO is a core Identity and Access Management component that streamlines authentication processes while enhancing user experience and organizational […]
Online marketplaces have changed how we shop. Now, we can easily find everything from unique items to everyday necessities with a swipe or a tap. Mercari has become a popular option in this space. Since launching in Japan in 2013 and coming to the U.S. in 2014, it has gained over 20 million monthly active […]
With the digital innovation on rise, it’s easy to hack or even snoop on someone’s computer and it’s easy to be target of search history hacking. Your internet service provider (ISP) can see everything you do online. They can see which websites you visit, what you search for and even who you talk to. In […]
If you’ve had enough of the constant calls and text messages from an unknown number and you are ready to hit the block button but you’re unsure how that works on an iPhone, don’t panic. With U.S. consumers receiving nearly 5 billion robocalls monthly in 2025 and Americans losing $29.8 billion annually to phone scams, blocking unwanted numbers […]
Cyber extortion is becoming an increasingly common form of cybercrime. According to a report by Cybersecurity Ventures, global damages from ransomware attacks are expected to surpass $30 billion annually by the end of 2025. This highlights the growing threat that ransomware poses to businesses and individuals alike. Cyber extortion is a serious threat that impacts […]
Medical identity theft is becoming a huge problem and is one of the fastest-growing types of fraud. In 2024 alone, more than 276 million healthcare records were either exposed or stolen in the U.S., according to a report from HIPAA Journal. This means that every day, hundreds of thousands of people are at risk of […]
If you have finally scored a PS5 and you’re ready to start gaming online with your friends, the only problem is you’re stuck with a strict NAT type and laggy multiplayer. Port forwarding your PS5 is actually pretty straightforward and will open up your connection in no time. In just a few steps, you’ll be […]
If you’ve decided to clear your router’s browsing history. Whether you share your network with others, want to free up space on the router, or value your privacy, deleting the router’s logs and history is essential. The good news is, clearing your router’s history is simple enough. The bad news is that the steps can […]
Ever get that annoying message on your iPhone that says “This network is blocking encrypted DNS traffic”? Yeah, it’s frustrating. What does it even mean and how do you get rid of it? Don’t worry, we’ve got you covered. See, your iPhone uses something called DNS, or Domain Name System to access websites. When it’s […]
In today’s digital landscape, identity theft has become more sophisticated and dangerous. Among the many types of identity fraud, synthetic identity theft is emerging as the fastest-growing and hardest-to-detect form. Unlike traditional identity theft, synthetic identity fraud involves the creation of entirely new identities using a mix of real and fictitious data, making it incredibly […]
If you’re a diehard basketball fan but your team just can’t seem to make the playoffs this year then all you want is to watch LeBron and the Lakers or Steph and the Warriors battle it out for a championship run. However, cable is crazy expensive and you’d rather not go to a crowded sports […]
You absolutely love watching live sports, but your cable bill keeps going up every year. There’s got to be a better way to stream all your favorite teams without breaking the bank. Well, Kodi has some killer add-ons that make cutting the cord easy while still getting access to tons of live sports events. In […]
If you’re tired of all those annoying ads on YouTube and want to upgrade to YouTube Premium, Great choice – you will get ad-free videos, access to YouTube Originals shows, and the ability to download videos to watch offline. The only downside is that YouTube Premium isn’t cheap at $13.99 per month. Don’t worry, you […]
Hackers behind the Akira ransomware now use a legitimate Intel CPU tuning driver to disable Microsoft Defender and bypass system protections. According to GuidePoint Security and a report by Bleeping Computer, attackers load the Intel driver rwdrv.sys, used by the ThrottleStop utility, and register it as a system service. It gives them kernel-level access. They […]
Researchers have uncovered a new malware campaign named GreedyBear. This campaign used over 150 malicious Firefox extensions to impersonate popular cryptocurrency wallets and steal more than $1 million in digital assets. Koi Security researcher Tuval Admoni confirmed the fake extensions posed as MetaMask, TronLink, Exodus, Rabby Wallet, and other well-known wallet services. Attackers used “Extension […]
As the world continues to advance technologically, cyber threats also continue to evolve. One of the most common threats on the internet is phishing attacks, which often involve the use of phishing links or URLs. URL phishing attacks are a serious threat that can result in losing sensitive information and financial loss. By being aware […]
With the rising privacy issues, it’s important to hide your location from strangers. There are several other reasons why you might want to change your browser location. Maybe you’re traveling and want to access websites that are specific to the country you’re visiting. Maybe you live in a country other than the one you were […]
Your device can join this criminal network without any visible signs. No pop-ups. No crashes. No obvious malware warnings. Botnets are designed to hide in plain sight, silently turning millions of innocent devices into weapons of mass digital destruction. According to Cloudflare, 71% of HTTP DDoS attacks in Q2 2025 were initiated by known botnets. Understanding […]
That innocent-looking device in your pocket? It’s recording your conversations, tracking your location, and sending your most private moments to complete strangers, all while you sleep peacefully, completely unaware. This is spyware and it’s already inside 1 billion devices worldwide. Right now, as you read this, advanced spyware is silently stealing data from phones, laptops, and […]
Privilege escalation is a critical security threat where attackers exploit system flaws to gain higher levels of access than originally authorized. Whether targeting a single device or an entire cloud infrastructure, such attacks can lead to full system compromise. In fact, according to IBM’s Cost of a Data Breach Report 2024, compromised credentials and privilege […]
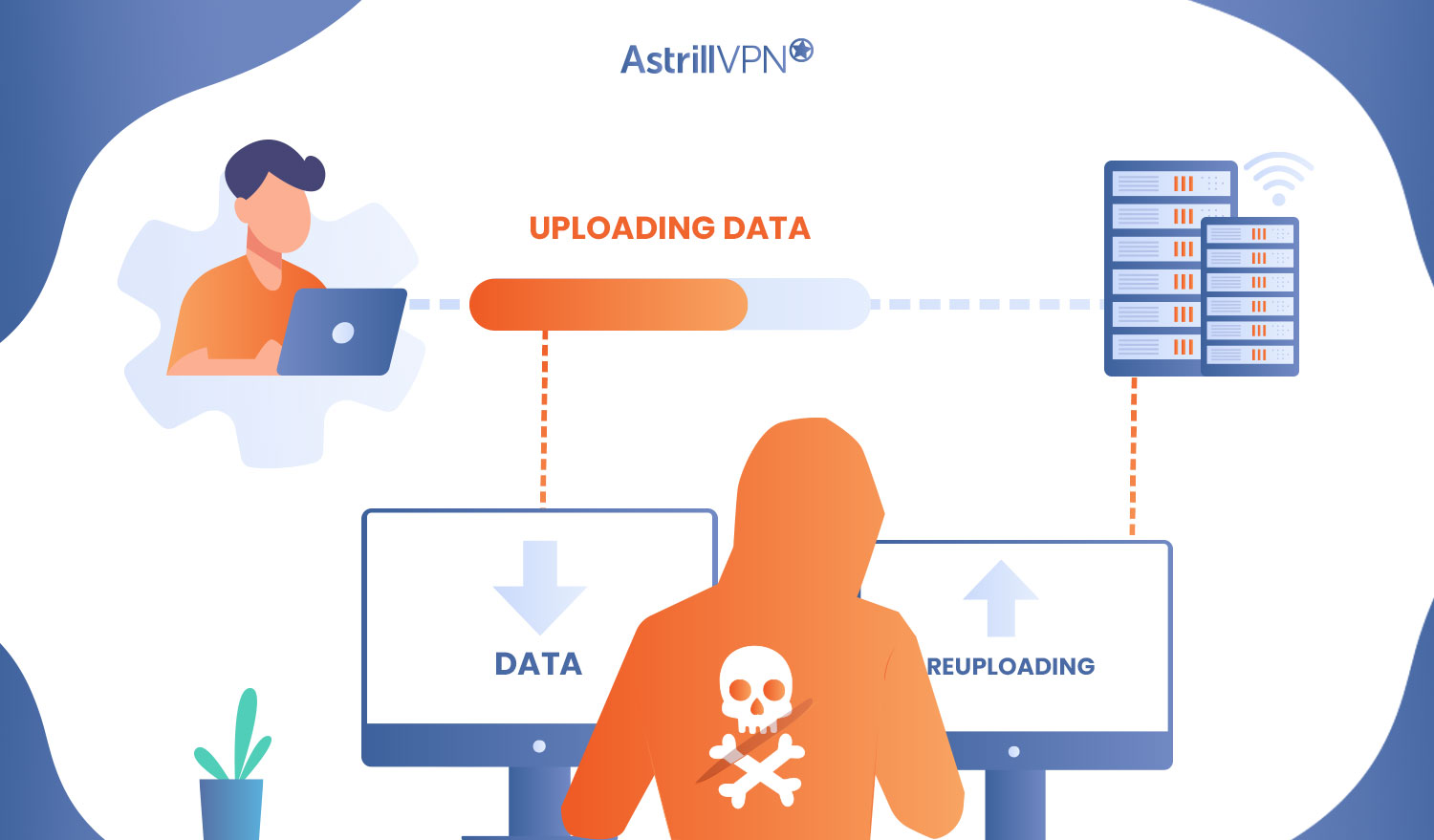
In the world of cybersecurity today, there are many different attack vectors to be aware of. One relatively common type is the replay attack. It sounds like something out of a sci-fi movie, but essentially, it’s when someone tries to “replay” a valid request or transaction on the web in order to gain access to […]
Have you ever received a suspicious phone call claiming to be from your bank or a government agency? Vishing, short for “voice phishing,” uses phone calls or voice messages to trick you into divulging sensitive information or taking harmful actions. As technology advances, these scams become increasingly sophisticated and challenging to detect. Understanding vishing and […]
The Internet of Things (IoT) has become deeply embedded in our daily lives, powering everything from smart homes and wearable health monitors to industrial automation and critical infrastructure. As of 2025, over 17 billion IoT devices are connected globally, which is expected to surpass 25 billion within just a few years. While this hyperconnectivity brings […]
Are you having trouble accessing the web interface of your Xfinity router because you can’t find the IP address? Don’t worry, we’re here to help! Most Xfinity routers come with a default IP address of 10.0.0.1. However, if you’ve made any changes to the default settings, locating the correct IP address becomes crucial for accessing […]
Ever get one of those tech support calls claiming to be from Geek Squad, offering to fix a problem with your computer? Yeah, those are scams. As much as we wish Best Buy’s tech support team made house calls, they don’t do unsolicited phone support. The truth is, there are shady characters out there trying […]
In cybersecurity, few threats are as deceptive and damaging as the Trojan horse virus. Named after the legendary Greek myth, this malware hides its true intent behind a seemingly legitimate facade. Once inside your system, it can steal data, monitor your activities, and even allow remote access to cybercriminals. In this article, we’ll explore everything […]
If you are an iPhone user considering using a free VPN on your beloved- device, we get it because who doesn’t love a good freebie? However, regarding your online privacy and security, is a free VPN the way to go? Before you hit that download button, let’s talk about what you’re getting (or not getting) […]
In today’s increasingly connected world, cyber threats are growing in frequency and sophistication. Organizations of all sizes face constant risks of unauthorized access, data breaches, and malware infections. One of the most effective ways to detect these threats before they cause severe damage is by using an Intrusion Detection System (IDS). IDS tools serve as […]
If you’re scrolling through Instagram and get serious travel envy from all the amazing photos your friends are posting from around the world and you also wish you could change your Instagram location and make it look like you’re somewhere more exciting than your hometown. Well, there’s an easy way to change your Instagram location […]
We know you’re obsessed with getting that Victory Royale in Free Fire, but high ping and lagging can really put a damper on your gaming experience. You’ve probably heard rumors that the best VPN for Free Fire like Astrill can help boost your connection speed and lower your ping for Free Fire. But does it […]
Cyber threats are no longer a future concern, they are the present reality. As we enter 2025, digital security is under siege like never before. With cyberattacks increasing in scale, complexity, and impact, organizations across every sector are forced to rethink their cybersecurity strategies. This blog explores the evolving threat landscape, significant trends, high-profile incidents, […]
In today’s digital age, you’re likely familiar with various cybersecurity threats. However, one increasingly prevalent danger may have escaped your notice: smishing. This malicious tactic combines “SMS” and “phishing“. Smartphones have made banking, shopping, and two-factor codes as easy as glancing at a text and exactly why cyber-crooks love smishing. In 2025, SMS-based phishing accounts […]
If you’re a diehard Knicks, Rangers, or Sabres fan but you cut the cable cord long ago and now you’re wondering how you’ll get your MSG fix this season without paying for a full cable package. Don’t worry, you’ve got options. Streaming services have changed the game so you can watch all your favorite teams […]
In today’s cybersecurity landscape, ransomware attacks have evolved into a lucrative and destructive industry, and LockBit is at the forefront of this digital menace. Since its emergence in 2019, LockBit has rapidly become one of the most active and dangerous ransomware families, responsible for a significant share of global cyberattacks between 2021 and 2025. With […]




















![What happens when you block a number on iPhone? [Updated]](https://www.astrill.com/blog/wp-content/uploads/2023/03/Feature-Image-27.jpg)







![How to get the Cheapest YouTube Premium Discount? [Updated]](https://www.astrill.com/blog/wp-content/uploads/2024/01/How-to-get-Cheapest-YouTube-Premium-Deals.jpg)









![The Truth About Geek Squad Scams: What You Need to Know? [Updated]](https://www.astrill.com/blog/wp-content/uploads/2023/09/The-Truth-About-Geek-Squad-Scams.jpg)








