With over 2+ billion users worldwide, WhatsApp is one of the most popular messaging apps, but that also makes it a major target for cybercriminals. While WhatsApp uses strong end-to-end encryption, hacking incidents are still rising due to scams, social engineering, and user mistakes rather than technical flaws. So, can someone hack your WhatsApp? The […]
Text messaging is one of the most common ways people communicate today, but it has also become a major target for cybercriminals. From fake delivery notifications to phishing links, scammers are constantly evolving their tactics. A common concern many people have is: can simply replying to a text message put you at risk? In this […]
As cryptocurrency adoption continues to grow worldwide, so do the risks associated with it. With billions of dollars stored in digital assets, cybercriminals are constantly finding new ways to exploit vulnerabilities in crypto systems. From exchange hacks to phishing scams, the need for strong crypto security has never been more critical. In 2025 alone, crypto-related […]
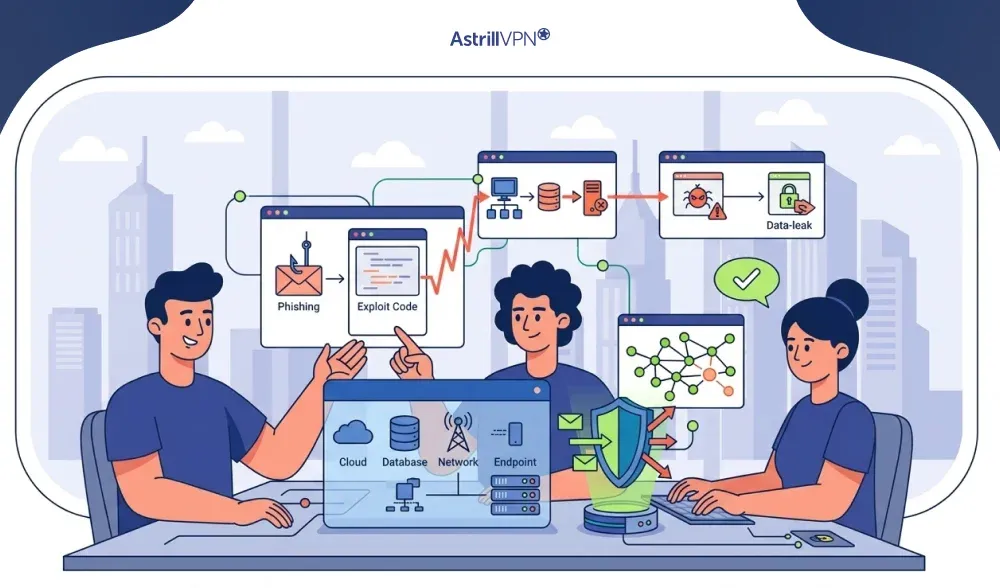
What is an Attack Vector and How to Avoid it
Every breach begins with a single point of entry. It might be a phishing email that seemed completely legitimate. It could be a password reused across multiple accounts. Or it could be a plugin on a company website that hasn’t been updated in two years. Whatever the cause, attackers find it and exploit it. These […]
Backdoors are one of the oldest and most persistent threats in cybersecurity. Backdoor attacks are not new, but they are growing. The data is sobering: Mandiant found backdoors in roughly 35% of malware families identified during incident response cases in 2024. Average breach costs involving backdoor access have climbed toward $4.7 million. And the average […]
With the rapid growth of cryptocurrency adoption, security has become a top concern for investors. According to industry reports, over $3 billion in crypto was stolen through hacks and scams in 2022 alone, underscoring the importance of secure storage solutions. This is where hardware wallets come in. A hardware wallet is considered one of the […]
HAK5 developed the Wi-Fi Pineapple, which is a private company. Now you may be wondering, how do fruit and WiFi go hand in hand? Well, there’s a story behind its name. The WiFi Pineapple gets its name from its appearance. It’s a small, black device with multiple antennas at the top that stem outwards in […]
Home computers have become the control center of our digital lives: banking, shopping, work, education, and even smart home controls all run through them. That convenience also makes personal devices a prime target for cybercriminals. From silent spyware to aggressive ransomware, threats today are smarter, faster, and often invisible. You don’t need to be a […]
Shein has gained a massive global following with its trendy and affordable apparel. However, concerns about data security, product quality, and ethical practices have led many people to question the safety of shopping on this platform. In this comprehensive guide, we will explore Shein’s security measures, past data breaches, and steps you can take to […]
As virtual meetings, online classes, and remote collaboration become the norm, video-conferencing platforms like Zoom have become essential tools for work, education, and social interaction. However, this rapid shift to digital communication has also opened the door to new forms of online abuse. One of the most disruptive and widely reported threats is Zoom bombing, […]
A script kiddie hacker is someone who performs hacking activities using tools, exploit kits, or automated attack software created by others. Instead of discovering vulnerabilities or building their own attack methods, they rely on publicly available scripts to scan targets, attempt logins, exploit known weaknesses, or disrupt services. The difference between a generic script kiddie […]
Cyber threats are evolving faster than ever, and one of the most challenging forms of malware security teams face today is polymorphic malware. Unlike traditional malware that uses a fixed code structure, polymorphic malware continuously changes its appearance, making detection extremely difficult. This ability to mutate allows it to bypass signature-based antivirus tools and remain […]
Digital payments are everywhere, from buying coffee to shopping online, and Apple Pay has become one of the most popular options. But with rising cybercrime, scams, and data breaches, a common question keeps popping up: Is Apple Pay safe? The short answer is yes, Apple Pay is considered one of the most secure payment methods […]
iPhones have a pretty solid security setup, which is why it’s not super common to see major malware issues like you might on other devices. But that doesn’t mean it can’t happen. Stuff like targeted spyware, dodgy configuration profiles, phishing scams, and unsafe downloads can still put your iPhone at risk if the right conditions […]
Social media has become an integral part of our daily lives, serving as a platform for our hobbies, entertainment, and even career growth as influencers. But bеwarе! The drеadful Instagram IP ban can dеstroy it all. No account accеss, zеro activity, and your businеss scrееchеs to a halt. But don’t panic, my friеnd! Wе’vе got […]
As artificial intelligence systems, huge language models (LLMs), become deeply integrated into applications, chatbots, and enterprise workflows, new security threats are emerging alongside their rapid adoption. One of the most concerning and least understood of these threats is prompt injection. Unlike traditional cyberattacks that target code or infrastructure, prompt injection attacks exploit how AI models […]
Instagram has introduced Vanish Mode to address privacy concerns among social media users. This feature gives individuals greater control over their messaging by enabling temporary, disappearing chats that mirror the ephemeral nature of in-person conversations. This guide will delve into the functionality and purpose of Instagram’s Vanish Mode, answering frequently asked questions about this privacy-oriented […]
Remote access is now essential to how businesses operate. From remote employees and traveling teams to cloud administrators and external partners, organizations rely on secure remote connections every day. But every remote connection also introduces risk. If it is not adequately protected, it can become a direct entry point for attackers. Remote access security focuses […]
As internet users increasingly depend on secure websites for activities such as banking, shopping, and communication, encrypted connections have become essential to cybersecurity. The Secure Sockets Layer (SSL), known as Transport Layer Security (TLS), is crucial for protecting sensitive data as it travels between users and websites. Attackers have developed methods to bypass this protection […]
In an age of digital transformation, Operational Technology (OT) systems, once isolated and safe from outside threats, are increasingly connected to modern networks for efficiency, analytics, and automation. This connectivity, while beneficial, has radically shifted the cybersecurity landscape for industrial environments. Today’s OT infrastructure is a prime target for sophisticated threat actors, and organizations bear […]
Every time you open a website, send a message, or log in to an account, your data travels across multiple networks before reaching its destination. Most of the time, that journey is invisible and secure. But when an attacker quietly inserts themselves into that path, the risks change fast. On-path attacks are one of the […]
Mac systems include built-in security protections, but they are not immune to malware. Threats targeting macOS have increased steadily, with attackers distributing adware, spyware, credential stealers, and remote access tools designed specifically for Apple devices. These threats often operate quietly, making detection difficult without deliberate checks. Knowing how to check for malware on Mac is […]
Cyberattacks today rarely rely on a single weakness. Modern breaches usually unfold in stages. An attacker phishes a user, escalates privileges, moves laterally, and quietly extracts data. This is precisely why single-layer security no longer works. Defense in depth is built on a simple but powerful idea: no single control should ever be trusted to […]
Artificial intelligence systems rely heavily on large volumes of data to learn patterns, make decisions, and generate accurate outputs. While this dependency enables powerful capabilities, it also creates a critical vulnerability known as data poisoning. Data poisoning attacks manipulate training or input data to compromise AI behavior, leading to biased predictions, incorrect decisions, or even […]
How to Remove PC App Store Adware on Windows
Many Windows users encounter unexpected pop-ups, slow system performance, or unfamiliar software called PC App Store, which is installed on their computers. While the name sounds similar to official app marketplaces, it often raises concerns about security and privacy. Users frequently ask whether PC App Store is a virus, how it entered their system, and […]
When you use a website, start a video call, or connect to a secure service, your data travels through various networks owned by internet providers, cloud services, governments, and businesses. BGP is the routing system that directs this data. BGP operates in the background, making rapid decisions about data paths. When it functions well, the […]
What is DNS Flood Attack: DNS flood DDoS attack
Modern internet infrastructure depends heavily on the Domain Name System (DNS) to function smoothly. Every time a user types a website address into a browser, DNS translates that domain name into an IP address. Due to their critical role, DNS servers are a prime target for cybercriminals. One of the most common attacks aimed at […]
Despite modern network defenses and best practices, Smurf attacks continue to surface in real-world DDoS traffic mixes and can still pose a threat when network configurations are weak or outdated. In simulated environments and real-world attack analyses in 2025, security researchers observed that a single Smurf-style packet sent to a misconfigured broadcast network could trigger […]
Ransomware attacks have evolved rapidly over the past few years, becoming more targeted, aggressive, and damaging. Among the most notorious threats was Maze ransomware, a strain that reshaped how ransomware campaigns operate. Maze was not just about encrypting files; it introduced data theft and public shaming as part of its attack strategy, pressuring victims into […]
Distributed Denial-of-Service (DDoS) attacks have evolved far beyond overwhelming networks with sheer volume of traffic. One of the most significant modern threats is the application-layer DDoS attack, also referred to as a Layer 7 DDoS attack. These attacks target the application layer of the OSI model, where web applications, APIs, and services interact directly with […]
In today’s digital age, where nearly every aspect of our personal and professional lives is connected to the internet, cybersecurity threats have become more sophisticated and dangerous. Ransomware stands out as one of the most disruptive and costly. Whether it’s a multinational corporation, a local hospital, or an individual user, no one is immune to […]
If you’ve recently encountered a message on your iPhone asking you to wait an hour before changing a password or other security setting, you’re not alone. This is Apple’s security delay feature, and it’s designed to protect your device from sophisticated theft tactics. In this comprehensive guide, we’ll walk you through everything you need to […]
A cyberattack occurs every 39 seconds, totaling over 2,200 attacks daily. Website owners face constant threats from hackers, and a single breach can cost thousands of dollars, erode customer trust, and significantly impact search rankings. This guide covers everything you need to protect your website: the vulnerabilities hackers exploit, the most dangerous current threats, and […]
Web browsers have become one of the most common entry points for cyberattacks. From phishing websites and malicious ads to drive-by downloads and zero-day exploits, attackers increasingly target browsers because they sit directly between users and the open internet. Traditional security tools such as antivirus software and URL filtering help, but they often fail against […]
A UDP flood attack is a type of Distributed Denial-of-Service (DDoS) attack that exploits the connectionless nature of the User Datagram Protocol (UDP) to overwhelm a target system, server, or network. By sending a high volume of UDP packets to random or specific ports, attackers consume bandwidth and system resources, causing slowdowns or complete service […]
Transport Layer Security, or TLS, is a protocol designed to secure digital communications. It ensures that data exchanged between a user and a server remains private, authenticated, and protected from tampering. Through TLS encryption, sensitive information such as passwords, messages, and financial details cannot be intercepted or read by unauthorized parties. TLS security relies on […]
Zelle is a popular payment platform with a staggering $806 billion transaction volume, a 28% increase from last year. It is also set to expand at a growth rate of 20% in the next five years. Zelle allows free instant transfers from the app. As companies strive to enhance the customer experience and make things […]
Pay-per-click (PPC) advertising is one of the most effective digital marketing channels, enabling businesses to drive targeted traffic and achieve measurable results. However, as online advertising continues to grow, so does one of its biggest threats: click fraud. This malicious activity drains ad budgets, distorts performance analytics, and weakens the effectiveness of paid campaigns. Whether […]
Most people think of stolen passwords or hacked servers when they hear about online security. But even something as simple as a domain name can decide if your business stays online or vanishes overnight. It might sound dramatic, but losing your domain can cause chaos. One minute, everything works. Next, your website redirects to a […]
Email remains one of the most widely used communication channels in the world, but it’s also a significant target for cybercriminals. From phishing scams to malware-laden attachments, spam emails pose serious risks to individuals and businesses alike. Industry estimates indicate that between 45% and 55% of global email traffic is spam, underscoring the importance of […]
When your browser says your connection is not private, it means it can’t confirm a secure link between your device and the website. This warning appears if security details are missing or unreliable, preventing the page from loading until you choose an action. Browsers do this to protect your data, since online security is now […]
When organizations review DDoS attack examples, they examine the events that have caused widespread outages, financial losses, and reputational damage. These cases help security teams understand how large DDoS attacks are constructed, how quickly they can escalate, and why each new wave often surpasses the one before it. The DDOS attacks force businesses to reassess […]
Spam bots are automated programs designed to flood online platforms with unwanted messages, fake accounts, or malicious links. Unlike useful bots that help with search engines or customer support, spam bots exist to exploit digital spaces for profit, disruption, or manipulation. They can target email inboxes, comment sections, social media feeds, and websites, often leaving […]
Secondhand shopping apps like Depop feel exciting because you can find rare vintage pieces, boost your income by reselling, or simply browse for something unique. At the same time, the risk of scams has grown. According to a consumer survey, 57 percent of Depop buyers reported being scammed over the past two years. Another report […]
The growing cybersecurity threats come in various forms, not all of them as overt as a full-blown virus. One prevalent and often insidious category is the Potentially Unwanted Program (PUP). These programs, while not always malicious in the traditional sense, can significantly degrade user experience, compromise privacy, and even create vulnerabilities. Recent reports indicate a […]
Is someone secretly listening to your phone calls, reading your messages, or tracking your location? In 2024, 2,297 legal wiretaps were authorized in the United States alone which is a 9% increase from the previous year and that’s just what’s officially reported. Unauthorized phone tapping by cybercriminals, suspicious partners, and corporate spies happens far more frequently, […]
In an era where data is arguably an organisation’s most valuable asset, ensuring that sensitive information remains secure and does not fall into the wrong hands has become a strategic necessity. The concept of Data Loss Prevention (DLP) is no longer just a buzzword; it is a cornerstone of modern data security programs. From protecting […]
Adware is one of the most common forms of unwanted software. It clutters your screen with pop-up ads, slows down your device, and can even track your online behavior. In the first quarter of 2025 alone, over 12.18 million mobile device attacks involving malware, adware, or unwanted apps were blocked by a major security vendor. […]
Spam calls are one of the most frustrating parts of modern communication. Whether it is a fake investment opportunity or a fraudulent tech support offer, these calls are designed to trick you into trusting the person on the other end. One of the most common tricks scammers use is making their number look local. You […]
As your organization operates online, it is constantly under siege from cyber threats, many of which evade detection until irreversible damage is done. Among the stealthiest is DNS hijacking, a technique by which attackers redirect your traffic to malicious sites, intercept sensitive data, or inject malware without raising alarms. According to DNSFilter’s 2025 Annual Security […]