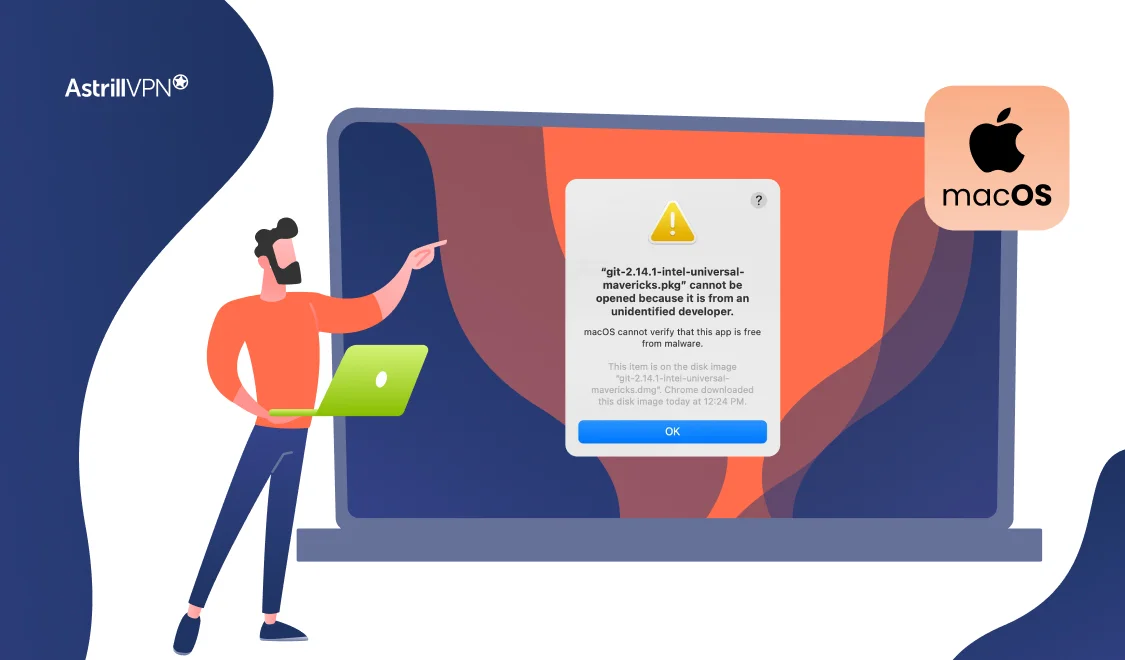
That moment when you try to open a new app and see the warning “macOS cannot verify that this app is free from malware” can be frustrating, but it’s also one of your Mac’s most important security features at work. This safeguard, powered by Apple’s Gatekeeper technology, isn’t just an arbitrary roadblock; it’s a critical […]
Users may show their support and acknowledge creators on TikTok with coins. Creators can rely on TikTok coins to generate money through virtual gifts they receive. Supporting creators financially and expressing gratitude for their work is as easy as buying coins and sending virtual gifts. So, how can you get cheap TikTok coins online? Follow […]
With a VPN, you can remain truly secure and protect your privacy whenever you’re online. Since digital security has become a growing concern, you may have questioned using a VPN. This article offers an explanation of VPNs and their benefits, as well as how to install one of the best VPN applications on the market. […]
Multiple security vulnerabilities in Jan AI, an open-source alternative to ChatGPT, have been discovered, which could potentially be exploited by remote, unauthenticated attackers to manipulate systems. This warning comes from Snyk, a developer security platform. Jan AI, developed by Menlo Research, is marketed as a personal assistant that operates offline on desktops and mobile devices. […]
Are you looking to unlock a world of free streaming content on your Amazon Firestick? Installing Kodi can open up endless entertainment possibilities, giving you access to movies, TV shows, live sports, and more. While the process may seem daunting initially, adding Kodi to Firestick is relatively straightforward when you follow the proper steps. In […]
Protecting online privacy has become more crucial in today’s digital landscape. Your IP address is a digital fingerprint, potentially exposing your location and online activities to prying eyes. Whether you’re concerned about cybercriminals, intrusive advertisers, or government surveillance, masking your IP address is a powerful way to safeguard your digital identity. This article will guide […]
In today’s digital world, staying anonymous can be trickier than it sounds. Everything from the websites you visit to the messages you send is tracked and recorded, often without your knowledge or consent. Achieving true online anonymity requires the right tools and techniques. This guide will show you how to protect your identity, remain anonymous […]
In today’s world, streaming platforms are a dime a dozen, offering users a wealth of content at their fingertips. One of the newer names in the world of free streaming is Tubi. With a vast library of movies, TV shows, and even some exclusive content, Tubi has garnered attention from viewers seeking free alternatives to […]
You might think using a VPN makes you completely anonymous while you browse the internet freely. But is that really the case? We’re often led to believe that cybersecurity and national security measures have our backs, but the reality is more complex. Despite claiming a no-logs policy, one of the UK-based VPN handed over user […]
In an increasingly interconnected world, the importance of online privacy and security cannot be overstated. As messaging apps become an integral part of our daily lives, the need for protecting our communications has never been more pressing. Telegram, a popular messaging platform known for its speed and security features, is used by millions worldwide. However, […]
The UK’s Information Commissioner’s Office (ICO) has provisionally fined Advanced Computer Software Group £6.09 million after a 2022 ransomware attack compromised the personal data of nearly 83,000 individuals. The breach disrupted critical NHS services, including NHS 111, and exposed sensitive information such as medical records and personal contact details. In August 2022, hackers exploited a […]
A new ransomware-as-a-service (RaaS) operation, named VanHelsing, has emerged, affecting multiple platforms including Windows, Linux, BSD, ARM, and ESXi systems. CYFIRMA first reported this new ransomware operation on March 7, and Check Point Research followed up with a detailed analysis yesterday. VanHelsing operates on a revenue-sharing model where affiliates keep 80% of ransom payments, with […]
If you are relocating internationally or have no idea how to change app store country, you may need to switch your country to access region-specific apps and content. Changing your App Store location isn’t as straightforward as expected, but you can navigate the process smoothly with the proper guidance. This step-by-step guide will walk you […]
In today’s digital age, protecting your privacy, data, and online identity is important. From online banking to online shopping and work-related activities, the internet is full of potential threats that could compromise your personal information. That’s why many people turn to VPNs (Virtual Private Networks) to stay safe while browsing the web. But there is […]
Data breaches are no longer rare occurrences but frequent and unsettling events that impact millions of users worldwide. In 2024 alone, companies like T-Mobile, LastPass, and Uber have faced significant data breaches, compromising vast amounts of personal information. These incidents serve as stark reminders of the vulnerability of our digital lives. Maintaining the privacy of […]
A sophisticated malware campaign known as ‘DollyWay’ has been actively exploiting WordPress websites since 2016, compromising more than 20,000 sites globally. Security researchers have identified that the malware’s primary goal is to redirect unsuspecting visitors to malicious websites, including fake dating, gambling, cryptocurrency, and sweepstakes platforms. The **DollyWay** malware infiltrates WordPress websites by exploiting vulnerabilities […]
If you have considered is opera gx good as your primary web browser then you are on the right track. As a gamer-focused variant of the Opera browser, it offers unique features tailored to enhance your gaming experience. However, before adopting any new software, it’s crucial to evaluate its security measures. We’ll delve into its […]
Google’s parent company, Alphabet, has agreed to acquire cloud security startup Wiz for $32 billion, marking its largest acquisition to date. The deal aims to strengthen Google Cloud’s cybersecurity capabilities to compete with Amazon Web Services and Microsoft Azure. Wiz, a rapidly growing startup, provides cloud security solutions across multiple platforms. Pending regulatory approval, the […]
Apple recently disclosed a security flaw in its Passwords app through its security content update that left users vulnerable to phishing attacks for three months before being addressed in the iOS 18.2 update. The issue, first spotted by security researchers at app developer Mysk, raised concerns about user data security, particularly for those accessing the […]
Nvidia has rolled out crucial security updates to address vulnerabilities in its Riva AI platform. If left unpatched, hackers could exploit its services for unauthorized access and potential financial damage. Riva, Nvidia’s GPU-accelerated speech and translation service, is widely used for real-time conversational AI applications, including large language models (LLMs) and retrieval-augmented generation (RAG). However, […]
Malicious actors have found a new way to exploit Cascading Style Sheets (CSS), which are primarily used for styling web pages, to bypass spam filters and invade users’ privacy. According to recent findings by Cisco Talos, these malicious tactics pose serious risks to both security and personal information. Omid Mirzaei, a researcher at Talos, noted […]
Firmware updates are often overlooked, yet they are as important as updating your smartphone’s operating system or your computer’s antivirus software. Router manufacturers release these updates to address vulnerabilities, improve performance, and introduce new features. Ignoring them can expose your network to cyber threats, slow your internet speed, or cause connectivity issues. A secure and […]
As cyber threats continue to evolve, your organization’s security depends on more than just technology. You and your employees are the human firewall in cybersecurity – the critical first line of defense against attacks. By cultivating security awareness and best practices across your workforce, you can significantly reduce vulnerabilities and prevent breaches. This article will […]
A baiting attack is a form of social engineering where cybercriminals use enticing offers or items to manipulate victims into compromising their own security. These attacks exploit human curiosity, trust, or greed, often leading to malware infections, data theft, or unauthorized system access. Understanding baiting attacks is critical to staying safe in an increasingly connected […]
The Wacatac Trojan virus can cause severe damage to your device and compromise your data if action isn’t taken. This virus specifically targets Windows devices; once it enters your device, it can compromise sensitive and confidential data. Suppose you suspect your computer device has been infected with the Wacatac malware. In that case, you must […]
As a technology professional, you’re likely familiar with various cybersecurity threats. However, one often-overlooked danger lurking in your systems could be macro viruses. These insidious programs hide within seemingly innocuous documents, waiting to wreak havoc on your network. The initial macro virus emerged in July 1995, and macro viruses, primarily targeting Word documents, quickly became […]
Internet Protocol Security (IPsec) VPN is one of the most robust solutions for ensuring secure, encrypted communication between devices over an IP network. For businesses, government agencies, or individual users, IPsec VPN is critical in safeguarding sensitive information from interception and tampering. In this guide, we will explain how IPsec VPN works, its key components, […]
If you’re looking for an alternative to VPNs, SOCKS5 proxies are an excellent option. Not all online privacy tools are created equal. While VPNs are great for encryption, SOCKS5 proxies offer a different set of benefits—like faster speeds and better performance for specific tasks. In this guide, we’ll explore the benefits of SOCKS5 proxies and […]
As you navigate the complex landscape of modern cybersecurity, understanding and combating network security threats is paramount. Your organization’s digital infrastructure faces an ever-evolving array of risks in today’s interconnected world. From sophisticated malware to social engineering tactics, the threats to your network’s integrity are diverse and relentless. This comprehensive guide will equip you with […]
Mega cloud storage limits users from downloading or transferring 5GB of data daily. If you need more than that, you have to wait 24 hours for the limit to be reset. To get around this, Mega offers subscription plans at different prices, letting you transfer more data daily. Additionally, there are tricks available to bypass […]
If you are wondering how to bypass vpn blocks, then you have come to the right place. Over time, VPN blocks have become a serious thing, and many online streaming platforms as well as many websites have started implementing VPN blockers. Even though a good VPN usually helps you bypass all barriers, it’s frustrating when […]
Comcast Xfinity is one of America’s biggest Internet Service Providers (ISPs). However, just because it’s one of the largest doesn’t mean it has a stellar reputation. Comcast has lately become notorious for throttling bandwidth and compromising the privacy of its customers. Comcast users experience slow internet connection since it throttles their bandwidth. We can imagine […]
Apple’s Safari focuses on keeping your privacy in check with features like Intelligent Tracking Prevention (ITP) and sandboxing to block annoying ads and cross-site tracking. However, you’re still not completely off the grid—your ISP can see your traffic, websites can find your real IP address, and geo-restrictions apply. That’s where a VPN for Safari comes […]
Kodi is a versatile, open-source media player that allows users to stream movies, TV shows, and live content seamlessly. While Kodi is available on various platforms, Roku does not natively support it. Unlike other streaming devices, Roku’s closed operating system prevents direct installation of third-party apps like Kodi. However, there are alternative methods to use […]
As a cybersecurity professional, you know the ever-present threat of malicious code. From stealthy malware to sophisticated ransomware, nefarious actors constantly develop new ways to infiltrate systems and wreak havoc. To stay ahead of these evolving threats, you need a comprehensive strategy for malicious code detection. This article will equip you with cutting-edge techniques and […]
Have you ever tried accessing a website from home, realizing your IP address has changed since your last visit? Or why businesses and online services always seem to have a fixed digital identity while yours keeps shifting? That’s because not all IP addresses function the same way. While network devices like servers, routers, and switches […]
Streaming media to your TV has never been easier than with a Roku streaming player. When coupled with an internet-enabled device, this streaming stick makes it possible to watch live video from any location. This is why Roku surpassed the 85.5 million active users milestone last month (Q3 2024). In this guide, we have lined […]
Are you concerned about your privacy and security while using Discord? As an avid Discord user, you understand the importance of protecting your online communications. With cyber threats on the rise, securing your Discord experience has become more crucial than ever. By using a virtual private network (VPN), you have a digital shield in the […]
LG Smart TVs have revolutionized how we consume entertainment, offering access to popular streaming platforms like Netflix, Hulu, Amazon Prime Video, and more, all from the comfort of your living room. However, much of the content on these platforms is geo-restricted, meaning you may not have access to certain shows, movies, or live broadcasts based […]
Traveling opens doors to new experiences and exposes you to significant cybersecurity risks. Nearly 20% of travelers fall victim to cybercrime abroad, often due to vulnerabilities like unsecured public Wi-Fi networks at airports, hotels, or cafés. These networks, while convenient, can quickly become a gateway for hackers to intercept sensitive information. Safeguarding your digital and […]
The United Football League season is ongoing, and we understand how much you’d be eager to watch it as a sports fan. However, the sad part is that many channels that broadcast UFL Football live are geo-restricted, and you may be unable to access them if you don’t reside in the United States. The United […]
If you are a tennis fan, you don’t want to miss a single volley or passing shot when Wimbledon rolls around next year. As the world’s oldest and most prestigious tennis tournament, Wimbledon is a must-see event. But for those of us not lucky enough to score tickets to Center Court, how can we get […]
Getting more privacy and security for your Xbox gaming is important these days. We all want to protect our info and play games safely. A virtual private network (VPN) is one of the best tools to make that happen. In this article, we’ll walk you through everything you need to know to get a VPN […]
In the digital age, your online security is paramount. Yet, lurking in the shadows of the internet is a threat you may not be aware of: packet sniffing. This powerful technique allows cybercriminals to intercept and analyze data transmitted over a network, potentially exposing your sensitive information. As you navigate the online world, understanding packet […]
Most countries have a variety of internet service providers to choose from, each with its own set of pricing packages, download limits, access methods, and routing technology. How to Check Your ISP? If you are wondering, “Who is my internet service provider” then you can follow these steps: Who Can See Your ISP? If you […]
IPL, the action-packed T20 cricket league, is renowned worldwide for its exciting matches and fierce competitions between teams like Mumbai Indians and Chennai Super Kings. Every year, the IPL attracts an astonishing viewership of around 505 million on television. However, if you’re an IPL fan in the USA, you might face restrictions when watching the […]
When protecting your privacy online, understanding what your Internet Service Provider (ISP) can see and how they monitor your activities is crucial. Many users believe that browsing in incognito mode or using a basic privacy tool is enough to keep their data hidden from prying eyes, but the reality is far more complex. ISPs can […]
Are you a traveler wondering how to use a VPN for cheaper flights? Using vpn to get cheaper flights may seem mythical, but in reality, it does work. We’ve made this detailed guide in order to explain how a VPN helps travelers book cheaper flights. Go through the guide thoroughly to understand every aspect related […]
Has your email account been compromised? Discovering that your email has been hacked can be a distressing experience. You may feel violated, anxious about what information was accessed, and unsure how to regain control. However, acting swiftly and methodically is crucial to mitigate potential damage and secure your digital presence. This step-by-step guide will walk […]
With an amazing user base of 35+ million, Cash App has undoubtedly transformed the world of mobile payments. But this transformation is limited to the people of the USA and the UK only! If you want to еxpеriеncе thе full potential of Cash App, thеn my friеnd, wе havе some good nеws for you. Today, […]

![How to Use a VPN: IN-depth Analysis and Guide [Updated]](https://www.astrill.com/blog/wp-content/uploads/2023/05/How-to-use-VPN.jpg)











![A Detailed Online Privacy Guide for Staying Safe on the Web [Updated]](https://www.astrill.com/blog/wp-content/uploads/2022/10/online-privacy-guide.jpg)

















![Install Kodi on Roku: Detailed Installation Guide [Updated]](https://www.astrill.com/blog/wp-content/uploads/2023/01/Feature-Banner-1.jpg)